如果配置了科学上网代理,一定要做免代理的配置,不然https访问会失败。
免代理配置
Docker免代理配置
[root@node1 harbor]#cat /etc/systemd/system/docker.service.d/http-proxy.conf
[Service]
Environment="HTTP_PROXY=http://10.0.0.1:7897"
Environment="HTTPS_PROXY=http://10.0.0.1:7897"
Environment="NO_PROXY=localhost,127.0.0.1,10.0.0.101,qazwsx.wsxedc.com"
重启docker
systemctl daemon-reload
systemctl restart docker
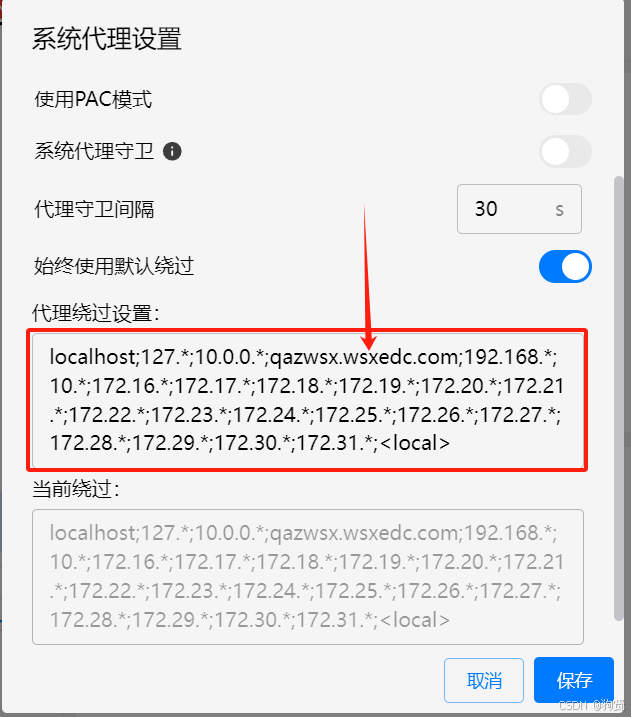
windows科学上网免代理配置
生成自签证书
#!/bin/bash
openssl genrsa -out ca.key 4096
openssl req -x509 -new -nodes -sha512 -days 3650 \
-subj "/C=CN/ST=Beijing/L=Beijing/O=example/OU=Personal/CN=RootCA" \
-key ca.key \
-out ca.crt
openssl genrsa -out qazwsx.wsxedc.com.key 4096
openssl req -sha512 -new \
-subj "/C=CN/ST=Beijing/L=Beijing/O=example/OU=Personal/CN=qazwsx.wsxedc.com" \
-key qazwsx.wsxedc.com.key \
-out qazwsx.wsxedc.com.csr
cat > v3.ext <<-EOF
authorityKeyIdentifier=keyid,issuer
basicConstraints=CA:FALSE
keyUsage = digitalSignature, nonRepudiation, keyEncipherment, dataEncipherment
extendedKeyUsage = serverAuth
subjectAltName = @alt_names
[alt_names]
DNS.1=qazwsx.wsxedc.com
EOF
openssl x509 -req -sha512 -days 3650 \
-extfile v3.ext \
-CA ca.crt -CAkey ca.key -CAcreateserial \
-in qazwsx.wsxedc.com.csr \
-out qazwsx.wsxedc.com.crt
直接运行上述脚本,ca证书和服务器证书都会生成在当前目录下
Harbor
修改Harbor配置
将harbor的证书配置指向上面刚生成的服务器端证书。
harbor关键配置如下:
# Configuration file of Harbor
# The IP address or hostname to access admin UI and registry service.
# DO NOT use localhost or 127.0.0.1, because Harbor needs to be accessed by external clients.
hostname: qazwsx.wsxedc.com
# http related config
http:
# port for http, default is 80. If https enabled, this port will redirect to https port
port: 80
# https related config
https:
# https port for harbor, default is 443
port: 443
# The path of cert and key files for nginx
certificate: /root/certificate/qazwsx.wsxedc.com.crt
private_key: /root/certificate/qazwsx.wsxedc.com.key
# enable strong ssl ciphers (default: false)
# strong_ssl_ciphers: false
重启harbor
./prepare
docker compose down -v
docker compose up -d
Docker
配置CA证书
创建目录,目录名字有特定要求,必须以域名命令,如果不是443端口还需要加上端口号,默认是443端口,所以一般不需要加。
/etc/docker/certs.d/
└── yourdomain.com:port
├── yourdomain.com.cert <-- 客户端证书,用于双向认证中的客户端认证
├── yourdomain.com.key <-- 客户端私钥,用于双向认证中的客户端认证
└── ca.crt <-- CA证书
这里使用的是单项认证,客户端的认证其实已经通过用户名,密码的方式认证了,配置案例如下:
[root@node1 harbor]#ls /etc/docker/certs.d/qazwsx.wsxedc.com/
ca.crt
docker默认会自动加载上述路径中的CA证书。
重启docker
systemctl daemon-reload
systemctl restart docker